User Accounts and Groups
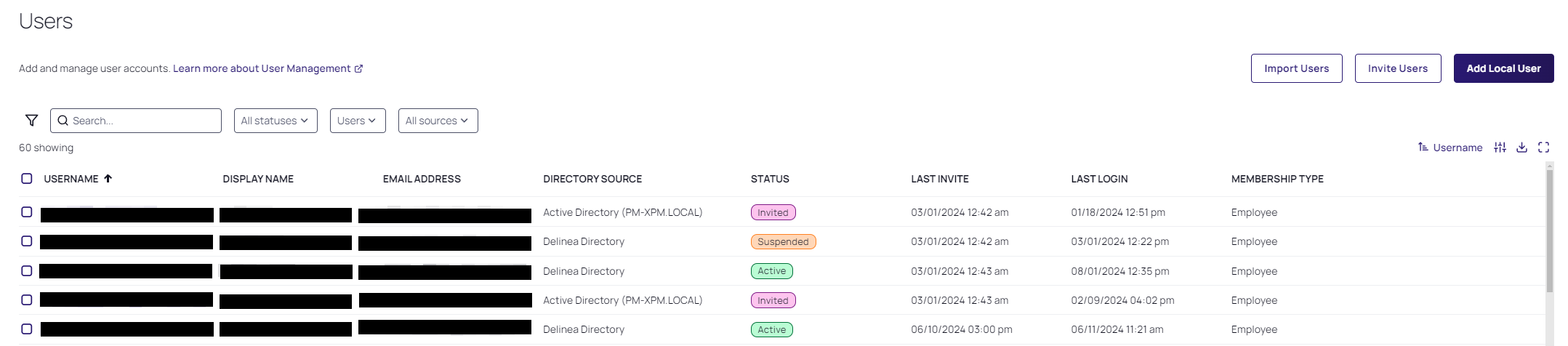
To manage users on the Delinea Platform, begin navigating to the Users page. The Users page displays all users on the platform, including Active Directory, Federated, Delinea Platform Directory (local), and Linux/UNIX users.
Click a USERNAME to go to that specific user's page, where you can view and edit settings for the user account, including the user's group memberships, roles, policies, activities, attributes, and audit trail specific to that user. For detailed instructions on managing Platform users, see Managing User Accounts.
Risk Score is displayed for each user. Risk is based on the analytics that generate non-resolved alerts and the associated findings. Risk scores are assigned as Low, Medium, and High. Refer to Analytics Findings and Risk.
| Risk Level | Definition |
|---|---|
| N/A | No risk has been identified for this user. Our monitoring systems have not detected any suspicious behavior or security concerns. |
| Low | Minor security alerts have been triggered for this user. These alerts are typically low concern and may result from legitimate activities, such as accessing resources from an unusual geographic location. No immediate action is required, but continued monitoring is recommended. |
| Medium | Elevated risk indicators have been observed for this user. This may include multiple alerts or behavioral patterns that warrant further investigation. While the situation is not critical, proactive measures, such as enhanced monitoring or verifying the user’s activity, are advised. |
| High |
Significant risk indicators have been detected for this user. Examples include:
For high-risk situations, the following actions are strongly recommended:
|
External User Accounts vs. Local User Accounts
Virtually every user account on the Platform should be an external user account, meaning either an Active Directory account or a federated account.
A local user account is added directly to the Platform by an administrator.
An external user account isn't added directly to the platform, but becomes accessible on the Platform when the associated Active Directory or federation is connected to the platform.
The administrator must still provide permissions to the user to access Platform features.
A local user must satisfy local authentication requirements to log in to the platform.
An external user must only satisfy the authentication requirements through the external source (AD or federation IdP).
A local user account appears on the Users page (Access > Users) when an administrator adds the account to the platform.
An external user account appears on the Users page only after the user logs in to the Platform for the first time.
Avoid Adding Local User Accounts
Adding local user accounts to the Platform is not considered a best practice for privileged access management. Local user accounts should be added only rarely, and for very specific purposes. For example, you might need to add a local user account for someone who needs to try out Platform functionality for a very limited time. Vendors are also added as local accounts. For details, see Adding Local User Accounts.
For related content, see the following:
Although the Platform uses the terms, IT User and Business User, these are not user classifications but rather license types.
For more information see User Classifications.