Computer Assets
The platform's Computers inventory provides an asset-centric view of all discovered computers in one place. From there you can efficiently manage and initiate remote sessions on your computer assets. To learn more about Secret Server’s discovery service, see Secret Server Discovery.
Inventory is available only for Platform instances connected to Secret Server Cloud. It is not available for customers using the Platform with Secret Server On-Premises.
Inventory Permissions
User access to the computer inventory is controlled by permissions. Platform admins can assign these permissions to manage full or targeted access, either across all computers or within specific collections.
-
To use the left navigation pane's Inventory menu to access inventory, users need the role permission View Inventory.
-
To see all computers, users also need the role permission View All Computers.
-
To give a user granular access to a set of computers, admins can make a collection and grant users permissions at the collection level. See Assigning User Permissions on Collections.
Your Computers Inventory
This section tells how to access a computer asset's basic and detailed information or launch a session into an asset.
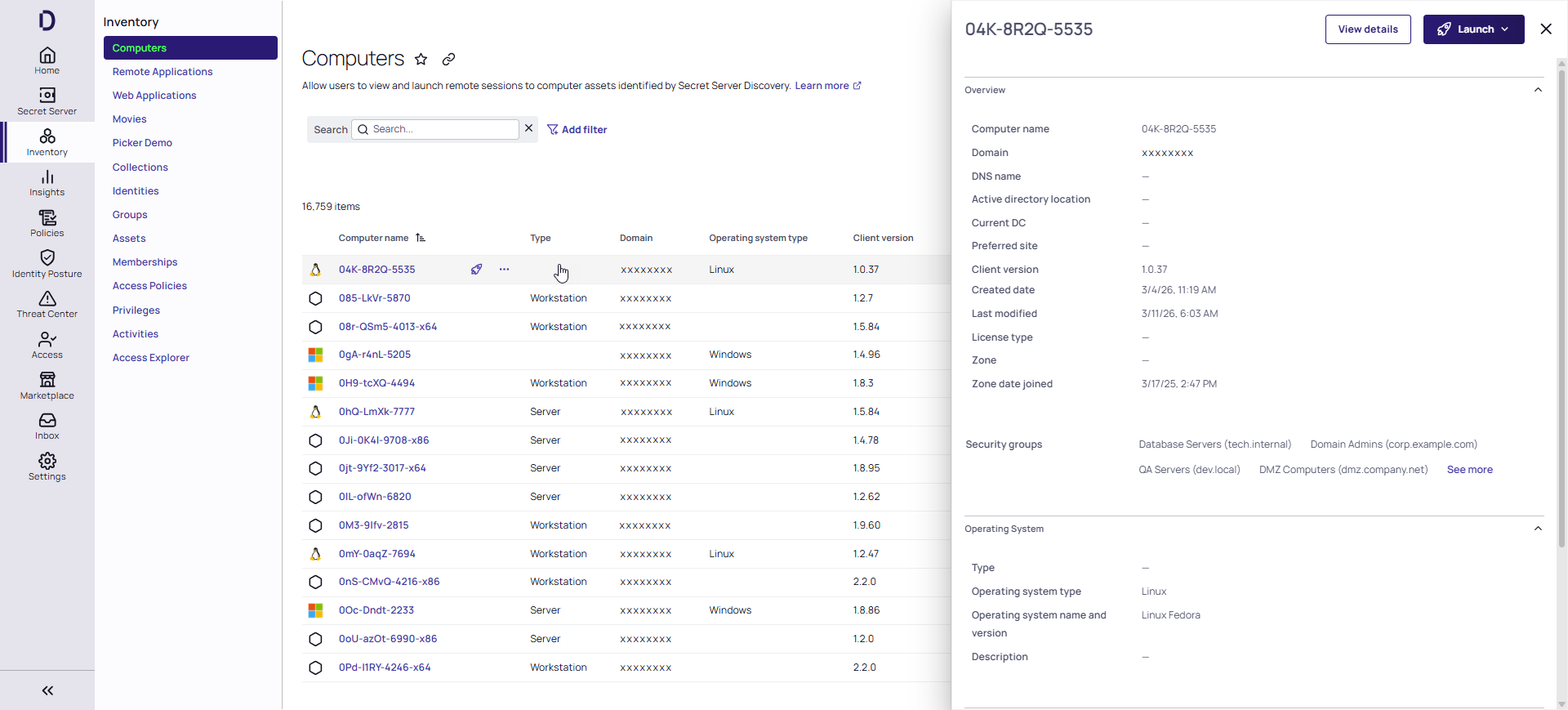
Once Secret Server discovery has been enabled and configured, you can view your Computers inventory through the Platform interface by selecting Inventory from the left navigation panel, then selecting Computers. The Inventory page displays a table with each computer asset in a row, and columns displaying basic information including the computer name, type, and domain. To control which data columns are displayed, click the column options icon just above the table on the right, and select or deselect boxes next to the column labels. To display a preview panel with details about a computer, click in any blank area in the row.
Inventory Search
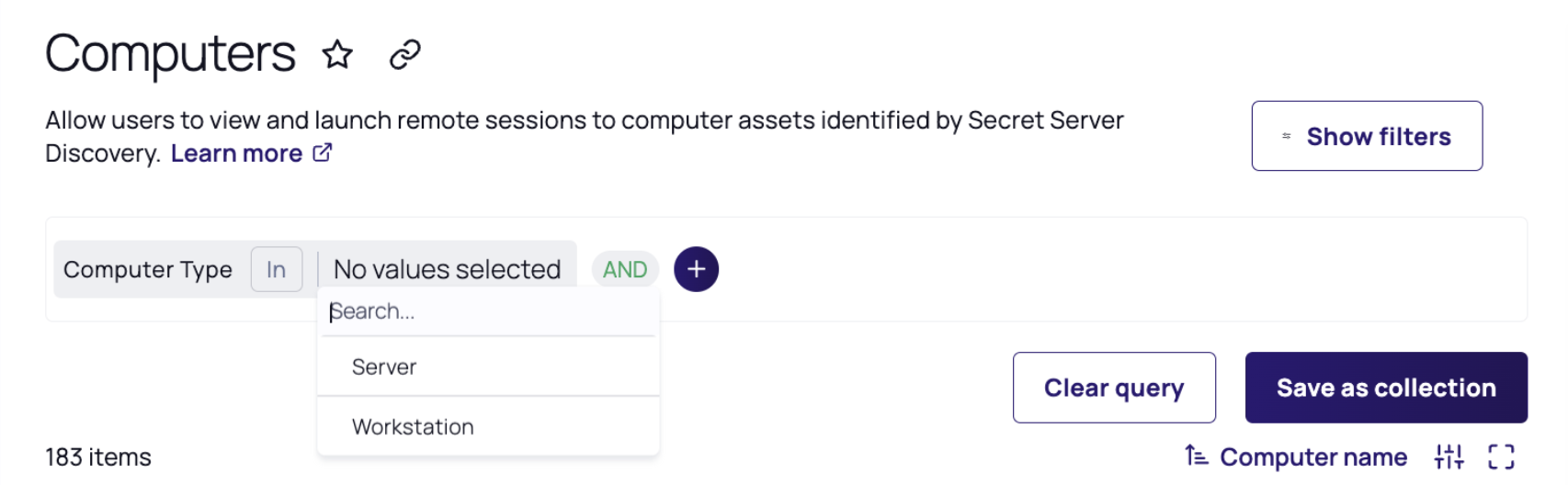
The query builder is an advanced search mechanism that you can use to create complex searches based on the information available. Click Show query builder in the Computers inventory page to open the query builder. For more information, see Using the Query Builder.
Details
If you click any empty space in a computer asset row, a panel opens on the right displaying details about the computer, such as the computer type, domain, DNS name, Active Directory OU, client version, and zone. The panel also displays links you can click to view more details or launch a remote session.
To see even more details, click the Details link in the panel. A page appears with more information about the selected computer. You can reach the same detail page by clicking the computer's name in the Inventory list. On the computer details page, the Details tab shows additional information, such as the preferred site and date the computer joined the zone.
The Policies tab (available to PCS customers only) shows which PCS policies include this computer as a target. See Task 10: Set Up PCS Policies.
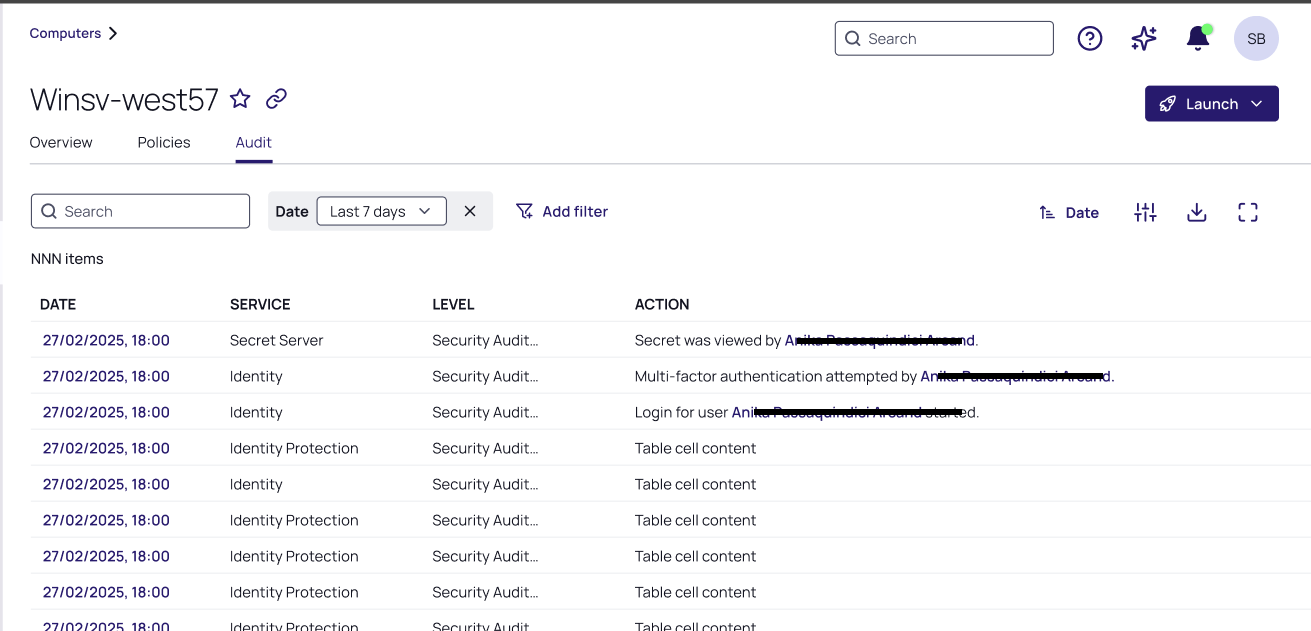
The Audit tab presents an audit trail specific to that asset (Computer Name). You can find the same entries in the Reviewing Audit Logs, filtered by its Target (Computer Name).
Logging In to a Computer
If you want to log in to (launch) a computer asset, click one of the launch options on the panel: Launch with Secret, Launch with My Account, or Launch with Manual Credential.
Launching with Secret
You can log on to any target system on the Delinea Platform by leveraging a vaulted credential from Secret Server. When selecting this option, vaulted credentials associated with that machine will appear and you will be prompted to select a secret to launch with.
Launching with My Account
You can log in to an enrolled Linux system with the same account you use to log in to the Delinea Platform, either from the Platform or by using a native application that uses SSH, SCP, or SFTP.
Launching with Manual Credential
Selecting Launch with Manual Credential allows you to launch manually in to a target system with a valid username and password. Depending on how authentication rules and authentication profiles are configured for the system and account, you might be required to respond to additional authentication challenges before logging on.
Disabling Active Inventory
To disable the inventory view, take the following steps:
-
Click Settings from the left navigation, then select Administration below Secret Server.
-
On the Secrets Administration page, click Platform Integration below Tools & Integrations. The Platform Integration page opens to the Configuration tab.
-
Click Edit.
-
Next to Forward Inventory Data to Platform, deselect the box. This action will prevent your tenant from incorporating newly detected computers. It will not impact any previously discovered computers.
PCS Policies
To meet your compliance requirements, you can assign policies precisely tailored to individual computers, ensuring that each asset operates securely and efficiently within your infrastructure. To learn more about assigning machine level policies, see PCS Policies.
For related content, see Grouping with Collections