Method 2: Using a Credential Resolver
With Secret Server Jenkins Integration, you can directly access and reference secrets in Secret Server. The integration uses the Delinea Secret Server Plugin in Jenkins to retrieve secrets from Secret Server and store them in the Jenkins global credentials store or in a folder in Jenkins.
Configuring a credential resolver in Jenkins involves the following tasks:
- Create a credential in Jenkins to store the username and password of the Secret Server application account. The Delinea Secret Server Platform Plugin uses the username and password of the Secret Server application account to connect to your Secret Server instance. For information about creating a credential in Jenkins, see Creating a Credential for the Delinea Secret Server Application Account.
- Create a credential resolver configuration in Jenkins.
Creating a Credential for the Secret Server Application Account in Jenkins
You must create a credential in Jenkins to securely store the username and password of the application account that you created in Secret Server.
To create a credential:
- Log in to Jenkins.
- From the Jenkins Dashboard, navigate to Manage Jenkins > Credentials > System > Global credentials.
- In the upper-right corner of the Global credentials page, select Add Credentials.
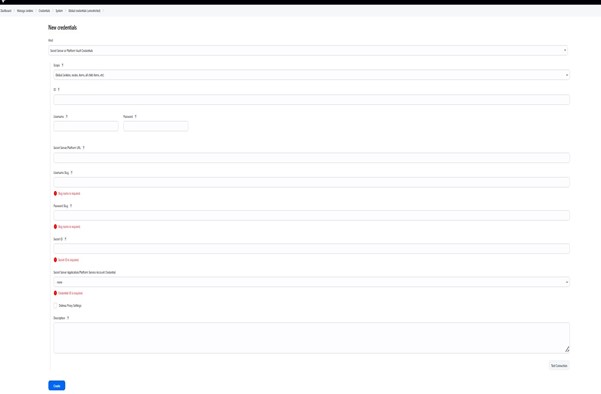
- In the New credentials dialog, provide the following details:
- Kind: Select Delinea Secret Server Application Account or Platform Service Account Credentials.
- Scope: Select Global or System.
- Username: Enter the username of the Secret Server application account.
- Treat username as secret: Select this checkbox to mask the username in build logs to prevent exposure of a confidential username. Clear the checkbox if you don't want to mask the username.
- Password: Enter the password of the Secret Server application account
- (Optional) ID: Enter a unique ID for the credential. If you leave this box blank, Jenkins will assign a globally unique ID (GUID) value to the credential as its credential ID.
- (Optional) Description: Enter a description for the credential.
- Select Create.
Creating a Credential Resolver Configuration
If you want to use a credential resolver in Jenkins to directly access and store secrets fetched from Secret Server , you must create a credential using kind of the Secret Server Vault Credentials type in Jenkins. The Secret Server Vault Credentials provides the credential resolver configuration needed to access a secret in Secret Server or Platform, including the URL of Secret Server, the username and password of the application account in Secret Server, and the secret ID.
By using the credential resolver configuration, the Delinea Secret Server Platform Plugin accesses the specified secret in Secret Server or Platform and retrieves the values of the specified secret fields (for example, username and password) into the corresponding fields in the credential resolver.
The Delinea Secret Server Plugin fetches only the values of the username and password fields in a secret or the values of equivalent fields, such as client id and client secret, from a secret that uses a custom secret template.
To create the credential resolver configuration:
- Log in to Jenkins.
- Navigate to Manage Jenkins > Credentials > System > Global credentials.
- Select Add Credentials.
- Select Delinea Secret Server Vault Credentials.
- Enter the following details:
- Scope: Select Global or System.
- (Optional) ID: Enter a unique ID for the credential. If you leave this box blank, Jenkins will assign a globally unique ID (GUID) value to the credential as its credential ID.
- Username: Leave blank (fetched automatically).
- Username Slug: Provide the slug name.
- Password: Leave blank (fetched automatically).
- Password Slug: Provide the slug name of the password field from the secret you want to retrieve from Secret Server.
- Secret Server URL: Provide the URL of your Secret Server instance
- Secret ID: Provide the secret ID.
- Secret Server Application Account: Select the username and password of the Secret Server application account or Platform service account from the credential that you created in Jenkins.
- Use Delinea Proxy Settings. If you are using Proxy server then check this checkbox:
- Proxy Host: Hostname or IP address of your proxy server.
- Proxy Port: Port number used by your proxy server.
- Username (optional): Proxy authentication username, if required.
- Password (optional): Proxy authentication password.
- No Proxy Host (comma-separated list): Comma-separated list of hosts that should bypass the proxy (e.g., test.secretserver.com, my-internal-server.com).
Username Slug must point to the secret field that holds the username or its equivalent. For example, if the secret uses a custom secret template with Client ID and Client Secret fields, provide the slug name for the Client ID field in Username Slug.
Password Slug must point to the secret field that holds the password or its equivalent. For example, if the secret uses a custom secret template with Client ID and Client Secret fields, provide the slug name for the Client Secret field in Password Slug.
Proxy Behavior
- All outbound network calls from the Delinea plugin use the configured Delinea specific proxy settings.
- If a username and password are provided, the plugin authenticates using those credentials.
- If No Proxy Hosts are configured and the target host matches any entry, the plugin bypasses the proxy.
- If the Delinea proxy is not configured, the plugin falls back to Jenkins Global Proxy settings.
- If both are configured, the Delinea Proxy Configuration is used.
- To validate the configuration and test the connection, select Test Connection.
If the connection is successful, a Connection successful message appears. Otherwise, an error message is display.
- 7. To access the secret from Secret Server after a successful connection test, select Create. The values of the specified secret fields are fetched from the secret into the Username and Password boxes, respectively, as shown in the image below.
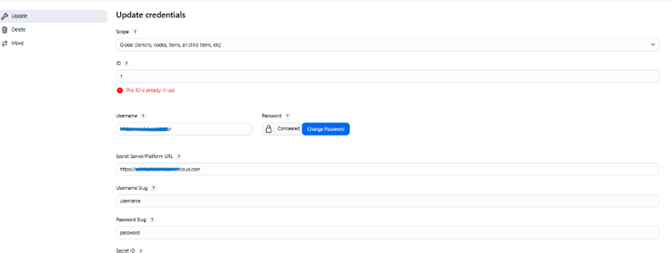
The fetched credentials are now stored in the credential resolver, and you can reference them in Jenkins by fetched username/password (password replaced with asterisks) wherever credentials of the type Usename/Password are required.