Configuring Jenkins Builds to Retrieve Secrets
These are the required configuration procedures to enable Jenkins to retrieve secrets from Delinea Secret Server or the Delinea Platform using the Delinea Secret Server Jenkins Plugin.
Step 1: Creating a Credential in Jenkins
You must create a credential in Jenkins to securely store the username and password of the application account or service user that you created in Secret Server or on the Delinea Platform. The Delinea Secret Server Plugin uses the Secret Server application account or the Platform service user credential to connect to your Secret Server or Platform instance.
To create a credential for the application account or Platform service user name and password:
- Log in to Jenkins.
- From the Jenkins Dashboard, navigate to Manage Jenkins > Credentials > System > Global credentials.
- Creating a credential in this path will store the Secret Server application account or Platform service username and password in the Jenkins global credentials store, which is accessible by all Jenkins users.
- In the upper-right corner of the Global credentials page, select Add Credentials.
-
In the New credentials dialog, provide the following details:
- Kind: Select Delinea Secret Server User or Platform Service Account Credentials.
- Scope: Select Global or System.
- Username: Enter the username.
- Treat username as secret: Select this checkbox as needed.
- Password: Enter the password.
- (Optional) ID: Enter a unique ID.
- (Optional) Description: Enter a description.
- Select Create.
Step 2: Use Cases for Retrieving Secrets During Jenkins Builds
Using Secrets in a Freestyle Project
- Log in to Jenkins.
- Select New Item.
- Enter a name, choose Freestyle project, and select OK.
- In the side panel, select Environment.
-
Enable Use Delinea Secret Server or Platform Secrets and provide:
- Secret ID: The ID of the secret.
- (Optional) Comment: If you configured the secret in Secret Server or the Delinea Platform to require a comment when accessing the secret, enter the comment that you want the Delinea Secret Server Platform Jenkins plugin to provide when accessing the secret.
- Environment Variables: One per secret field (for example, username, password).
- Application/Service Account Credential: The credential created earlier.
- Secret Server/Platform URL: The URL of your instance.
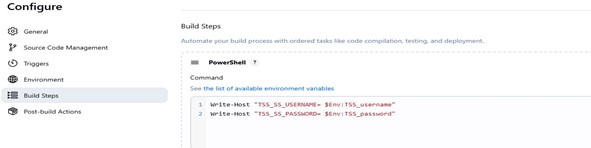
- In the Build Steps section, add a PowerShell or Bash step using TSS_-prefixed variables.
The Freestyle project view page opens. You can now run the project to fetch secrets from Secret Server automatically.
Using Secrets in a Jenkins Pipeline
-
Using Globally Defined Credentials and URL
- Navigate to Manage Jenkins > System > Delinea Secret Server/Platform.
- Select the default credential.
- Enter the Secret Server/Platform URL.
Example Pipeline Script:
Copypipeline {
agent any
stages {
stage('Print Secret Fields') {
steps {
withSecretServer(secrets: [[
id: 'SecretId',
autoComment: 'Comment',
mappings: [
[field: 'username', environmentVariable: 'username'],
[field: 'password', environmentVariable: 'password']
]
]]) {
bat '''
echo Username: %TSS_username%
echo Password: %TSS_password%
'''
}
}
}
}
}
If you configured the secret in Secret Server or the Delinea Platform to require a comment when accessing the secret, set
autoCommentto the comment that you want the Delinea Secret Server Platform Jenkins plugin to enter when accessing the secret.
-
Using Secrets in a Multibranch Pipeline
A Multibranch Pipeline retrieves secrets from Secret Server or the Delinea Platform through the Jenkins file stored in the repository.
- Log in to Jenkins.
- Create a Multibranch Pipeline.
- Configure a Git/GitHub repository as the Branch Source.
- Add credentials if the repository is private.
- Validate the repository connection.
Example Jenkinsfile:
stage('Fetch secrets from Delinea') {
steps {
script {
withSecretServer(secrets: [[
id: 'SecretId',
credentialId: 'CredentialId',
baseUrl: 'Secret Server or Platform URL',
mappings: [
[field: 'username', environmentVariable: 'username'],
[field: 'password', environmentVariable: 'password']
]
]]) {
echo "Secret fetched successfully"
}
}
}
}
Step 3: Configuring Delinea Proxy Configuration (Optional)
If your environment uses a proxy, configure Delinea-specific proxy settings:
- Navigate to Dashboard > Manage Jenkins > System > Delinea Secret Server/Platform.
-
Configure:
- Proxy Host
- Proxy Port
- Username (optional)
- Password (optional)
- No Proxy Hosts (comma-separated)

Proxy behavior:
- All plugin outbound calls use Delinea-specific proxy settings.
- If credentials are provided, the plugin authenticates.
- If host matches No Proxy Hosts, proxy is bypassed.
- If Delinea proxy isn't configured, Jenkins global proxy applies.
- If both exist, Delinea proxy overrides.
Step 4: Configuring Folder-Specific Credentials (Optional)
This topic describes how to store credentials in a specific folder in Jenkins so that only authorized users can access those credentials. The topic also describes how to give users folder-level permissions to the folder that contains the credentials. These steps involve Jenkins-specific configuration settings and are not related to the plugin itself.
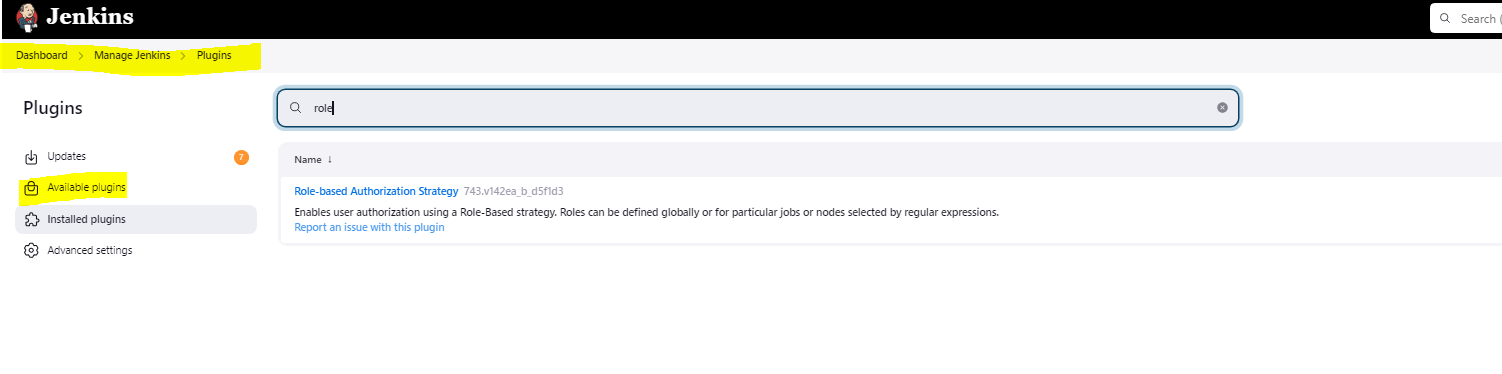
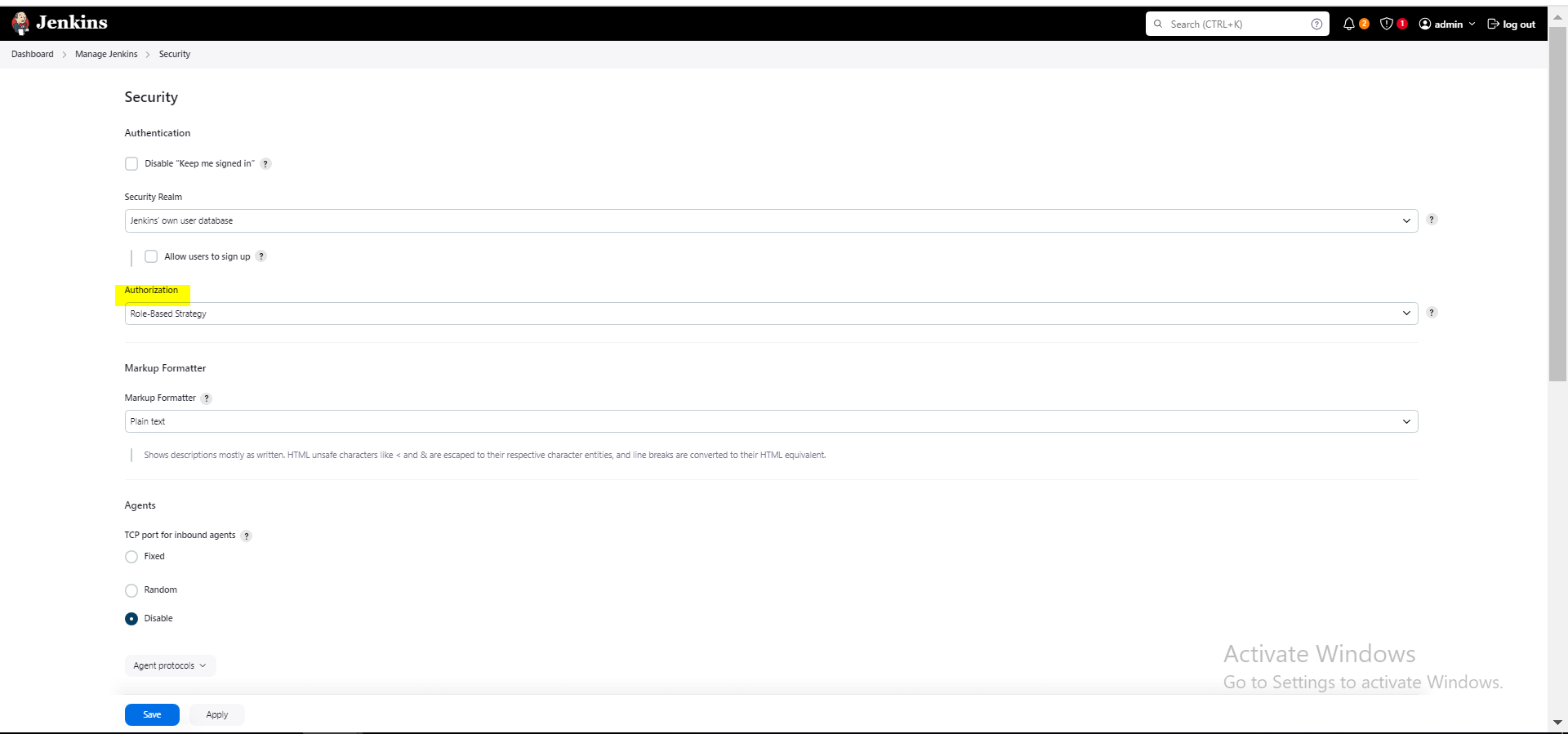
You must install the Role-Based Strategy in Jenkins. By using the Role-Based Strategy plugin, you can effectively manage folder-level access and permissions for credentials, ensuring secure and organized credential management.
Configuring folder-level access involves setting up appropriate folder-level roles and permissions in Jenkins and assigning those roles to users.
To configure folder-specific credentials:
-
In Jenkins, create the folder where you want to store the credentials.
Below is an example of a Credential Resolver configuration. You can also configure folder-specific
credentials for use during builds.
-
From the Jenkins Dashboard, navigate to the created folder and then navigate to Credentials > Folder > Global credentials.
-
On the folder-specific Global credentials page, create a credential to store the Secret Server application account or Platform service user username and password or create a credential resolver configuration.
For detailed instructions on how to create a credential resolver configuration, see Step 2: Use Cases for Retrieving Secrets During Jenkins Builds (begin from step 3).
-
Install the Role-Based Strategy plugin:
-
Enable role-based strategy:
-
Set up the folder-level roles and permissions:
-
Navigate to Manage Jenkins > Manage and Assign Roles > Manage Roles.
-
Under the Global roles section, select Add to create a new role and assign it to the Overall > Read permission.
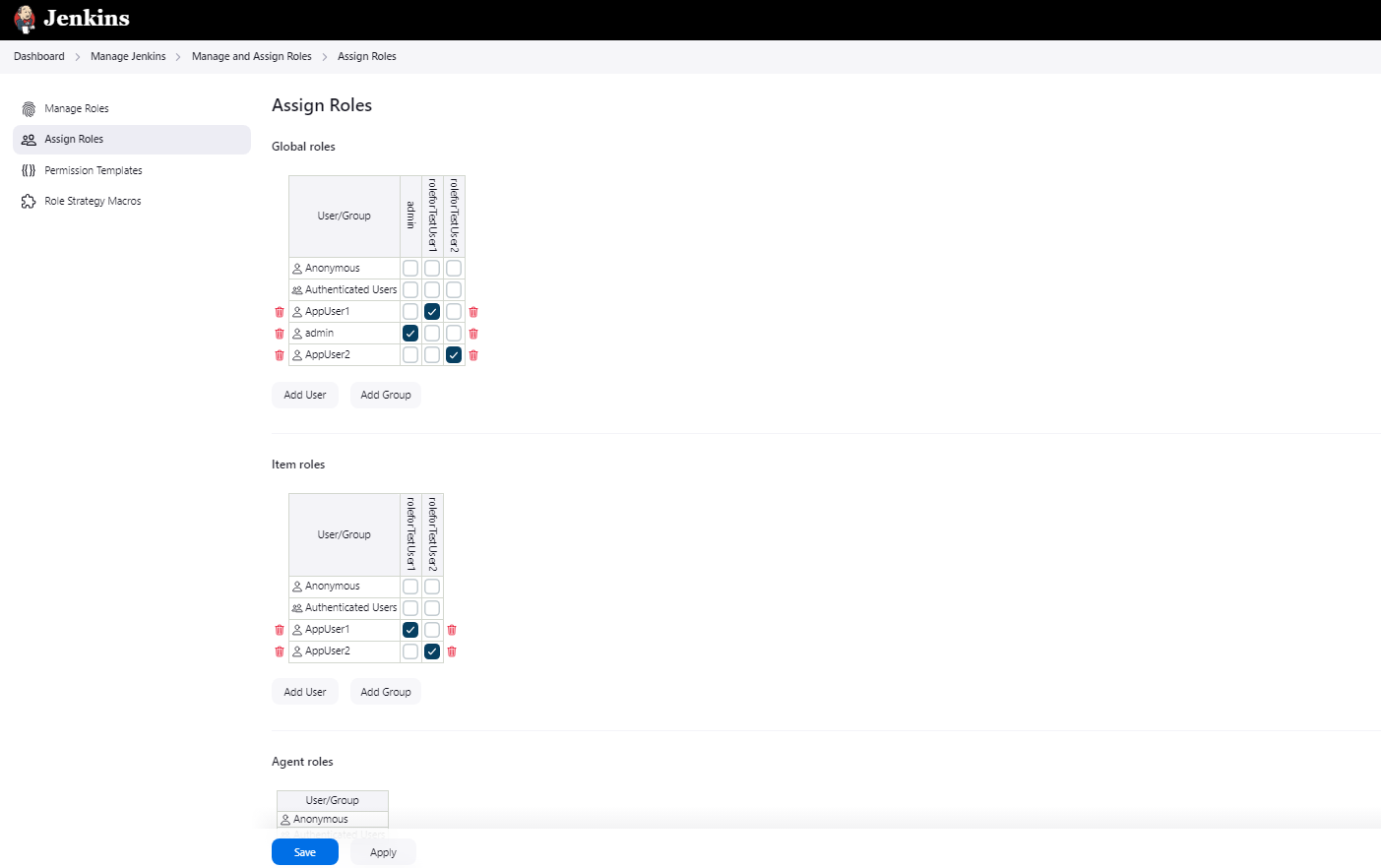
The image below shows example roles "roleforTestUser1" and "roleforTestUser2."
-
Under the Item roles section, assign the roles at least the Create Credentials permission and other required permissions (for example, Read, Build, Configure) and specify folder patterns in the Pattern column to apply them to specific folders.
The folder pattern must match the folder name. The image below shows the folder patterns for example "AppUser1" and "AppUser2" folders.
-
Select Save.
-
-
Assign the roles to users or groups:
-
Navigate to Manage Jenkins > Manage and Assign Roles > Assign Roles.
-
Assign the roles to users or groups as needed.
-
Select Save to save the role assignments to users or groups.
Now only the users and groups that have these folder-level roles can access the secrets stored in the folder.
-