Delinea Credential Cache Architecture
High-Level Workflow of Delinea Credentials Cache
The architecture supports deploying multiple Delinea Credentials Cache instances across different servers or Distributed Engines. Each instance operates independently and maintains its own local cache.
Credential cache relies on a Time-to-Live (TTL), which is 10 minutes by default. Once the TTL expires, the next request for the same secret will always fetch the updated value from Secret Server. If a secret is rotated within the TTL window (i.e., within 10 minutes), the cache returning the old value is expected behavior. Cache stores any secret that is requested via the API. It is not limited to MID Server credentials. The Credentials Cache supports multiple integrations.
Workflow Steps
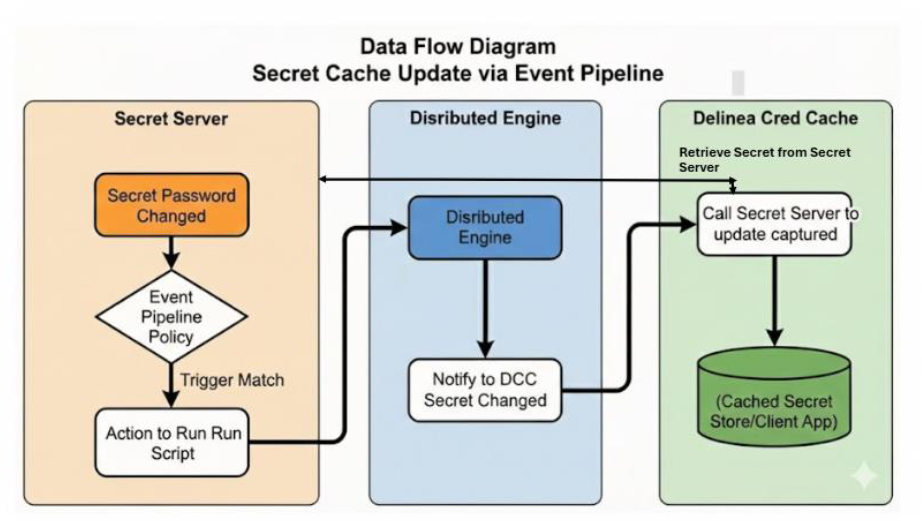
Event Fires
Example:
- The system changes a secret password
Event Rule Matches
- Action: Run Script
Run Site Is Evaluated (Secret Server)
Event Pipeline Behavior:
- The system detects secret changes
- The system triggers PowerShell script execution
- The system notifies all configured sites
Each Credentials Cache instance then independently retrieves the updated secret and refreshes its local cache.
Site Evaluation Rules:
- The system considers only Distributed Engines registered to the selected Site
Script Execution
- The system sends the job only to Distributed Engines within the selected Site.
- If multiple Distributed Engines exist in that Site:
- One healthy Distributed Engine picks up the job.
- The engine fetches the secret and updates the cached secret.
Each deployment operates independently without dependency on other cache instances.
Multiple Credentials Cache Instances
Delinea Credentials Cache can be installed on multiple servers or Distributed Engines simultaneously. This allows for region-wise or environment-wise deployments, where each server hosts its own Credentials Cache instance.
Each installation operates independently and maintains its own local cache. When an Event Pipeline is configured, all relevant Credentials Cache instances receive secret updates through the PowerShell script execution on their associated Distributed Engines.
When Event Pipeline–based secret updates are configured, all deployed Credentials Cache instances receive the update trigger and independently fetch and cache the updated secret. If Credentials Cache is installed on multiple Distributed Engines, each instance independently receives the update trigger and refreshes its local cache.
Load Balancing and Synchronization
Delinea Credentials Cache does not require load balancing or cache synchronization between instances.
Each Credentials Cache instance operates independently and retrieves secrets directly from Secret Server or the Delinea Platform when the Event Pipeline notifies it.
Best practices:
- If multiple Credentials Cache instances are deployed (for example, region-wise), each instance retrieves and caches the updated secret independently.
- There is no central synchronization mechanism between cache instances. Instead, each cache instance fetches secrets directly from Secret Server or Delinea Platform when notified.
- Always deploy at least two Credentials Cache instances to avoid single-instance unavailability and ensure high availability.
- Use Event Pipelines to trigger secret updates consistently across all instances.
Consistency Across Regions
The system achieves consistency through:
- A centralized source of truth (Secret Server or Delinea Platform)
- Event Pipeline–based notifications
When a secret changes, all deployed cache instances receive the update trigger and independently retrieve the latest value from the source system.
High Availability
If a Credentials Cache instance becomes unavailable:
- Other Credentials Cache instances continue to operate normally
- There is no impact on the overall system or secret availability
When the unavailable instance comes back online, it retrieves secrets during the next update trigger or through an on-demand refresh.