Continuous Identity Discovery
Continuous Identity Discovery (CID) enables you to readily discover privileged identities such as administrator, shadow admin, and service accounts that pose potential security risks. These include accounts that are stale, lacking MFA requirements, or lacking vaulted credentials in Secret Server. CID then prompts you to make specific corrections. CID runs automatically and continuously so you can easily monitor and secure privileged accounts.
The Continuous Identity Discovery (CID) feature was previously named Cloud Identity Discovery.
CID extends the discovery capabilities of Secret Server Cloud on the Delinea Platform, and represents a subset of the platform ITP/PCCE (Identity Threat Protection / Privilege Control for Cloud Entitlements) capabilities, including the following:
-
Inventories: Inventories provide a centralized and comprehensive view of all identities, groups and assets across an organization's cloud services and applications. They offer visibility into privileged accounts based on permissions, roles, groups, and federations. The definitions of privileged accounts and groups are customizable and can be updated as needed.
-
Checks: Checks enhance IAM hygiene through continuous monitoring of identity misconfigurations and over-privileging by, for example, detecting privileged users and suggesting vaulting for them.
The Delinea Platform provides checks for both CID and ITP/PCCE, but you might have access to CID checks without access to the ITP/PCCE checks. ITP/PCCE provides more checks focused on identity misconfiguration, application-specific configuration, IdP misconfigurations, and AI agents-specific checks, as well as threat detections like privilege escalation in AWS, brute force/MFA bombing.
See also:
-
The complete list of available CID Checks
-
The complete list of available ITP/PCCE Checks
Overview
This overview describes the high-level processes for getting started with CID by establishing a clean, actionable baseline for managing privileged and non-privileged accounts.
Step 1: Add CID Sources
Start by connecting CID to the identity sources you want to monitor. These sources can include Active Directory, Azure AD, AWS, GCP, and more.
-
Navigate to the Discovery page.
-
Select Sources.
-
Select Create Source.
-
On the Create discovery source page, select the relevant connectors and configure them with the required permissions
Adding more sources gives CID a broader view across your environment, improving correlation accuracy.
Once a source is integrated, initial data fetching can take about 24 hours.
Step 2: Review Checks for Non-Vaulted Entities
Once your sources are connected and data fetching completes, CID begins to surface accounts with potential security issues. Begin by reviewing entities that are not yet vaulted, and either vault them or exclude them.
See Diagnosing Issues with the Checks Panel.
Step 3: Establish a Baseline
After vaulting and excluding relevant accounts, you'll be left with a smaller set of accounts that haven't been reviewed yet. These are the undecided cases.
This forms your CID baseline—a clean state where all known accounts are either managed, excluded, or pending review.
Step 4: Customize Privileged User Definitions
With Continuous Identity Discovery, you can update your definitions of administrator and privileged accounts. Use this flexibility to tailor the platform discovery to your organization’s specific needs.
CID uses default definitions for Privileged and Admin accounts. If these don’t match your organization’s standards, you can update them:
-
From the left navigation menu, select Inventory.
-
Navigate to Collections > System.
-
Modify or create custom system collections that define what constitutes a privileged or admin account
For more details, see Collections.
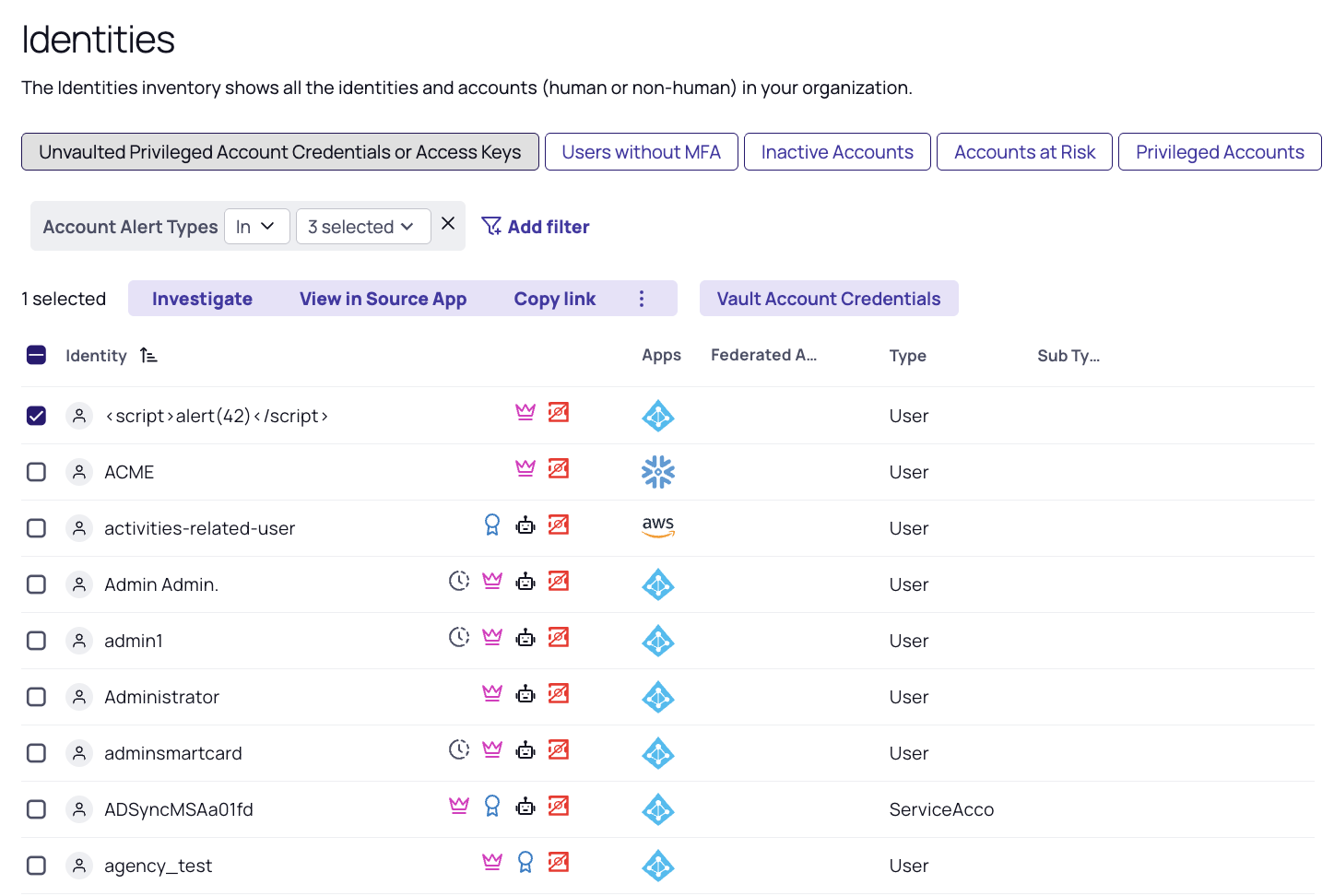
Step 5: Use Inventory for Advanced Filtering and Reporting
For deeper insights or customized views:
-
From the left navigation menu, select Inventory.
-
Select Identities.
-
Use filters to view accounts by type, source, vault status, and more.
-
Vault directly from this view or define reports for specific scenarios.
This feature is ideal for compliance audits, scheduled reviews, or identifying gaps in account coverage.
Next Steps
Once you’ve established your CID baseline:
-
Periodically review CID alerts and account recommendations
-
Adjust your exclusion and vaulting decisions as systems evolve
-
Leverage reporting and filters to monitor for drift or new privileged accounts
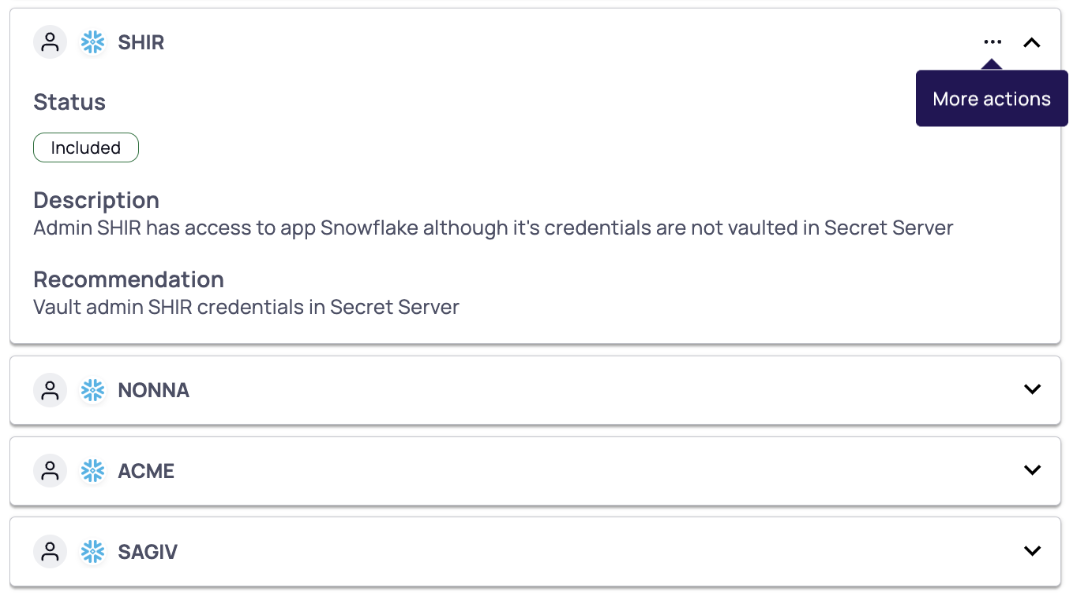
Discover Unvaulted Privileged Cloud Service Users
CID Discovery continuously identifies privileged cloud service users that are not yet vaulted in Secret Server Cloud. We recommend vaulting these accounts in Secret Server to enforce proper login, or disabling the user if access is unnecessary.
To discover privileged accounts not managed in Secret Server, select Identity Posture > Checks and review the following checks:
-
Unvaulted Admin Credentials
Discover cloud service administrators whose credentials are not in Secret Server. -
Unvaulted Shadow Admin Credentials (for CSP only)
Discover cloud service shadow admins whose credentials are not in Secret Server. -
Unvaulted Privileged Account Credentials
Discover privileged cloud service user accounts whose credentials are not in Secret Server. -
Unvaulted Admin Access Keys (for AWS only)
Discover cloud service administrators whose access keys are not in Secret Server. -
Unvaulted Shadow Admin Access Keys (for AWS only)
Discover cloud service shadow admins whose access keys are not in Secret Server. -
Unvaulted Privileged Account Access Keys (for AWS only)
Discover privileged cloud service user accounts whose access keys are not in Secret Server.
CID checks identify privileged accounts that are not vaulted based on the provided default templates. Custom templates, however, are not supported. As a result, secrets stored using custom templates may be incorrectly flagged as not vaulted.
Supported Applications
The Delinea Platform currently supports checks for unvaulted privileged accounts, admins, and shadow admins for the following applications:
-
Active Directory
-
AWS
-
Azure
-
Entra
-
GCP
-
Okta
-
Snowflake
-
Workday
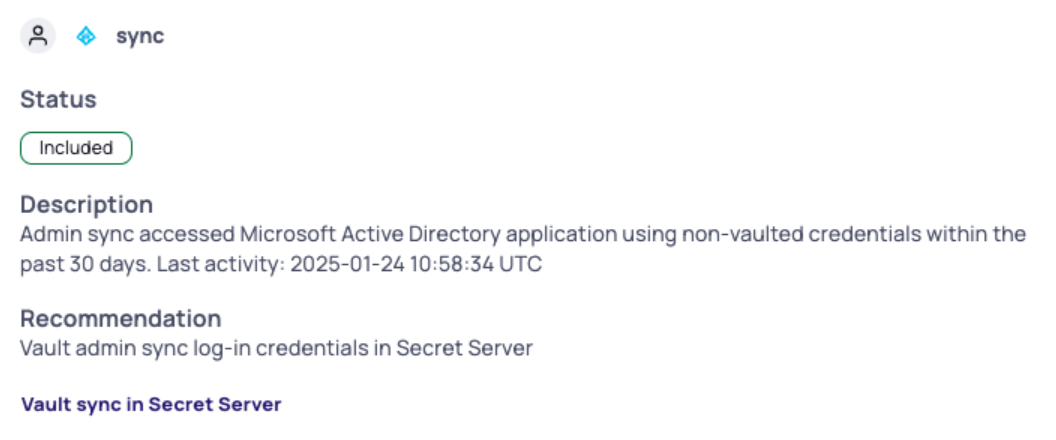
Discover PAM Bypassing
The Delinea Platform provides a mechanism to detect privileged accounts that bypass Secret Server by logging directly into cloud applications using access keys or login credentials. This detection is based on Identity and Access Management (IAM) activities and involves several checks to identify such bypassing activities.
The PAM bypass detection process involves the following steps:
-
Activity Collection: Activities from cloud applications are collected in near real-time. The detection check runs every few hours, allowing results to be available within a few hours. These results are retained for 30 days, after which any detected PAM bypassing alert will automatically resolve.
-
Comparison with Secret Server: When a new activity is detected, it is compared with the Secret Server Cloud (SSC) to determine if the account is vaulted. This involves checking the account's activity logs to identify who accessed the applications and whether the account is vaulted.
-
Check Execution: To discover cloud privileged accounts bypassing Secret Server, select Identity Posture > Checks and review the following checks:
-
Unvaulted PAM Bypassing Using Access Keys (for AWS only). Identifies accounts using unvaulted access keys to bypass Secret Server. Alerts are generated if accounts have vaulted access but opt for non-vaulted access.
-
Unvaulted PAM Bypassing Using Credentials. Identifies accounts using unvaulted credentials to bypass Secret Server. Alerts are generated if accounts have vaulted access but opt for non-vaulted access.
-
Vaulted PAM Bypassing Using Access Keys (for AWS only). Identifies vaulted accounts bypassing Secret Server using access keys, indicating possible use of shared or cached credentials.
-
Vaulted PAM Bypassing Using Credentials. Identifies vaulted accounts bypassing Secret Server using credentials, indicating possible use of shared or cached credentials.
-
-
Alternative Authentication Methods: For unvaulted accounts, the system checks if there are alternative authentication methods (such as credentials or access keys) that are vaulted. If such a method exists but the account still logs in using unvaulted credentials, it indicates bypassing of the vaulted authentication method and PAM itself.
Supported Applications
The Delinea Platform currently supports PAM bypass checks for the following applications:
-
AWS
-
Entra
-
Okta
-
Snowflake
Discover Delegated Permissions
CID will also discover accounts with delegated administrative permissions, such as delegated permissions for resetting passwords or delegated full permissions within an Organizational Unit (OU).
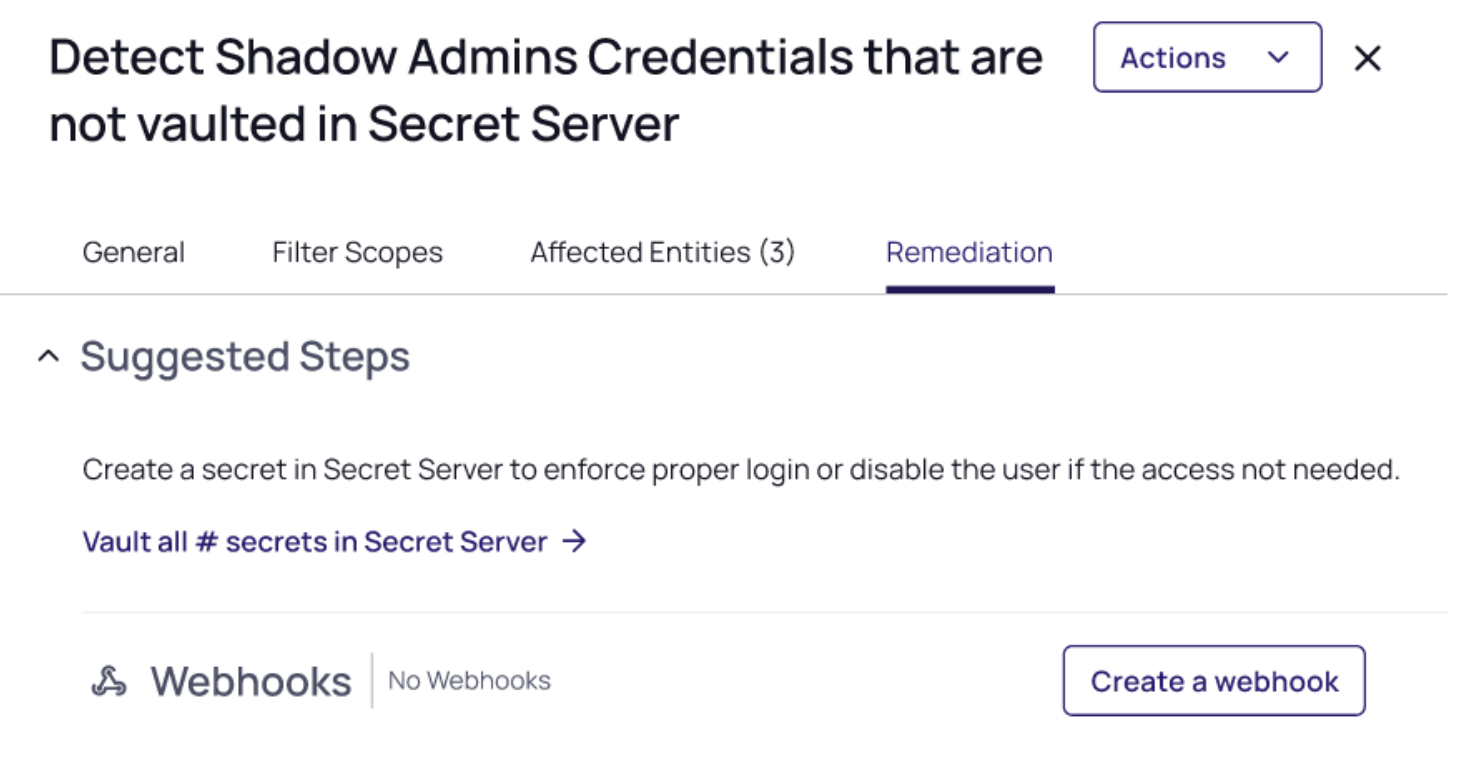
CID Manual and Bulk Vaulting
Once you have discovered all privileged cloud service accounts in your environment, you can close the loop and vault these accounts in Secret Server Cloud.
You can use manual vaulting or bulk vaulting:
Manual vaulting – You can select a specific account and vault it in Secret Server Cloud using the ellipsis. For more details, see Creating Secrets.
Bulk vaulting – You can vault all discovered cloud service accounts for a specific application in one click.
For a specific checks (see Discover Unvaulted Privileged Cloud Service Users above):
-
Click the Remediation tab
-
Click the link to vault all accounts in a click of a button
-
The Import modal will open and you will have to fill in some details.
For more details, see Manually Importing Local Accounts.
Vaulting from Inventory
For advanced use cases, you can also create custom queries within the Identities Inventory to search for all or a specific subset of entities, and vault them directly from there.
The vaulting option is available under Identities Inventory → Accounts tab.
Only unvaulted identities (indicated by the red icon) can be vaulted.
Creating a CID Report
Create a scheduled report to see all privileged accounts that are not vaulted along with additional information about them (account name, source app, privilege type, last login, and more). Using this report you can get all accounts that are not vaulted over time to your email and track remediation progress.
To create a report:
-
Click Insights from the left navigation menu.
-
Click Reporting.
-
Click Schedule a Report.
-
Create a new report with a name, frequency, and email recipients from the type, Unvaulted Privileged Accounts.
-
Click Create.
Learn more at Recurring Reports
ITP-PCCE-CID Integrations
The following topics explain how to set up ITP, PCCE,and CID integrations with the Platform.