Duo Authentication
This topic describes how to add a Duo MFA challenge to Platform login. After entering their password, users see a Duo prompt (push notification, passcode, etc.) before gaining access.
The following procedures require copying and pasting information between Cisco Duo and the Delinea Platform. Open both applications before you begin, and keep both open until you finish.
For details on enabling MFA on the Delinea Platform, see Creating Identity Policies.
Support Scope
The Delinea Platform supports Duo in one officially validated configuration:
Duo as an MFA provider — Platform can prompt users for Duo multi-factor authentication during login. This works the same way Duo MFA works in Secret Server. Configuration steps are documented and supported by Delinea Support. Customers who want Duo-based login should configure Duo as an MFA provider, not as a federated IdP.
The
Duo Application Types and Authentication Profiles
Duo offers two application types that integrate with the
| Duo Application | Auth Profile Challenge | Credentials | Description |
|---|---|---|---|
| Web SDK | Duo Universal Prompt | Client ID, Client secret, API hostname | Duo's current recommended integration. Uses a browser-based redirect flow to present the Duo Universal Prompt, which supports the full range of Duo authentication methods including WebAuthn/FIDO2 security keys. Provides a customizable, mobile-friendly experience. |
| Partner Auth API | Duo Auth API | Integration Key, Secret Key, API hostname | A server-side authentication flow. This is a legacy integration pattern that may be required for non-browser-based authentication scenarios. |
Administrators should create the Duo application that corresponds to the authentication challenge they plan to use. To use both authentication challenges, create both Duo applications.
Duo recommends the Universal Prompt (Web SDK) for new integrations. For more information, see the Duo Universal Prompt documentation.
Prerequisites
-
On the Delinea Platform, an administrator must be a Platform Admin or have a role with the following permission:
delinea.platform/identity/admin/manage -
In Duo, an administrator must have access to the Duo Admin Console with permissions to protect applications and create users.
Build a Universal Authenticator Duo Application
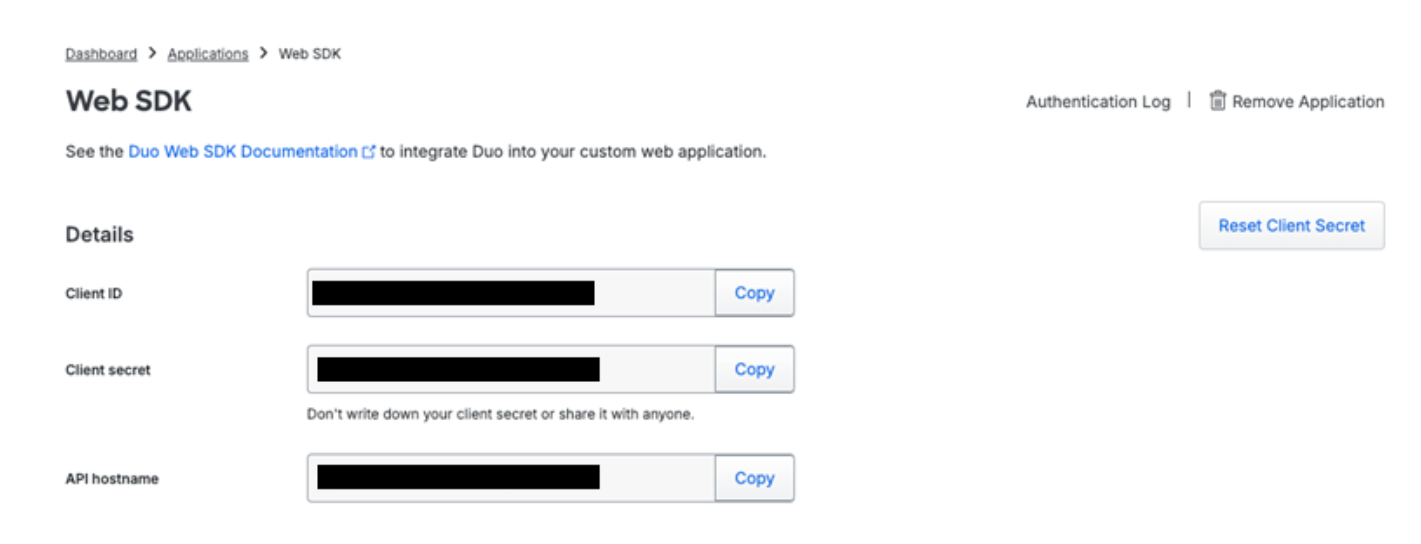
This procedure creates the Web SDK application in Duo. The credentials generated here are used when an authentication profile is configured with the Duo Universal Prompt challenge type.
-
In the Duo Admin Console, navigate to Applications.
-
Select Add Application.
-
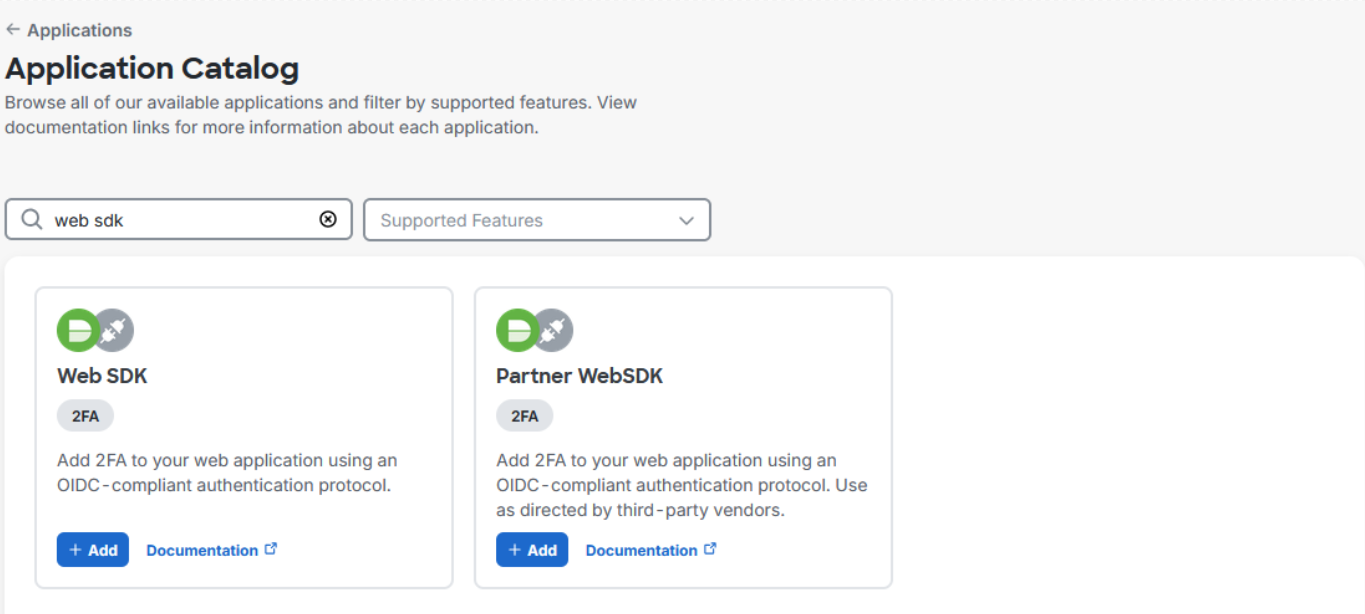
Filter the list of applications by entering
Web SDK. -
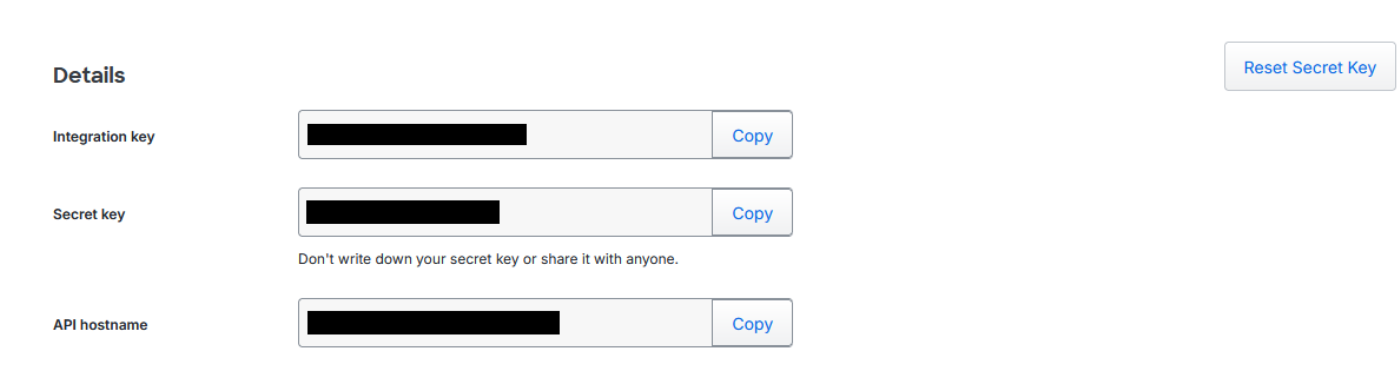
Copy and save the Client ID, Client secret, and API hostname. These values are required to configure Duo authentication on the Delinea Platform.
-
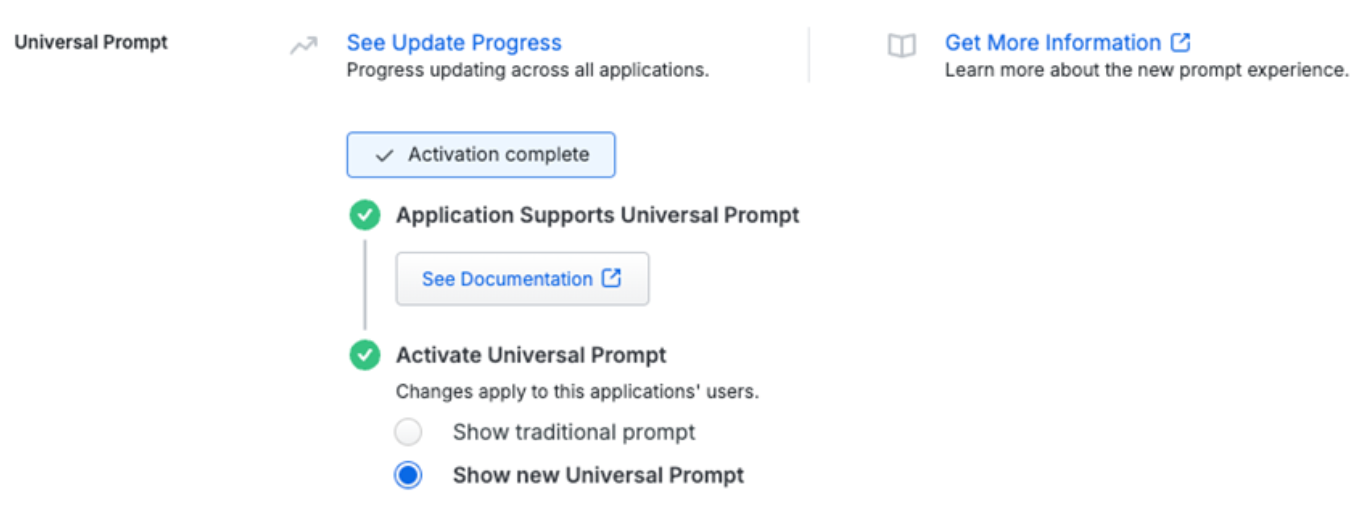
Under Universal Prompt, ensure that Show new Universal Prompt is selected.
-
(Optional) Configure policies per your requirements. Also see Duo Policies below.
-
(Optional) Configure settings per your requirements. To enable self-service, see Duo's Self-Service Portal documentation.
-
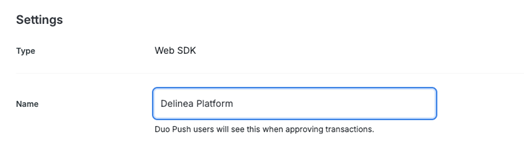
Navigate to the Settings section and update the Name field to something users recognize, such as Delinea Platform.
-
Click Save.
Build an Auth API Duo Application
This procedure creates the Partner Auth API application in Duo. The credentials generated here are used when an authentication profile is configured with the Duo Auth API challenge type.
-
In the Duo Admin Console, navigate to Applications.
-
Select Add Application.
-
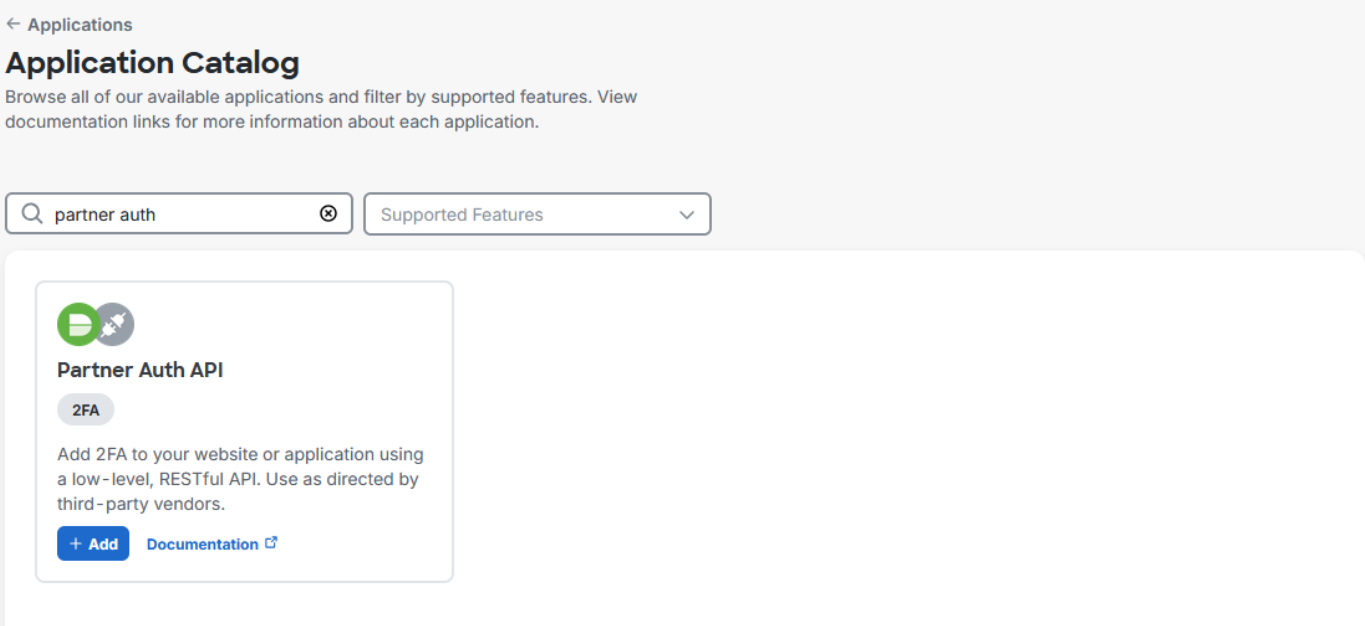
Filter the list of applications by entering Partner Auth API.
-
Copy and save the Integration Key, Secret Key, and API hostname. These values are required to configure Duo authentication on the Delinea Platform.
-
(Optional) Configure policies per your requirements. Also see Duo Policies below.
-
(Optional) Configure settings per your requirements. To enable self-service, see Duo's Self-Service Portal documentation.
-
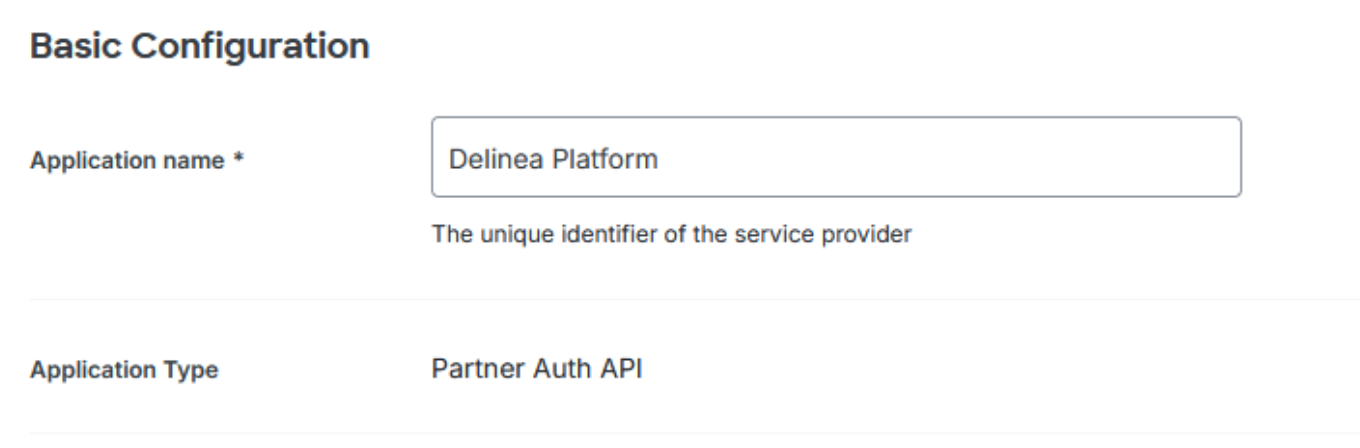
Navigate to the Basic Configuration section and update the Name field to something users recognize, such as Delinea Platform.
-
Click Save.
Add Duo to the Platform
Add Duo as an MFA Provider
-
Log in to the .
-
Navigate to the MFA Providers page.
-
From the Add Provider button, select Duo.
-
On the Add Duo page:
-
Enter a name.
-
Set the state to Enabled to activate the integration.
-
Ensure that the Duo Auth API configuration type is selected.
-
Enter the Integration Key copied from Duo.
-
Enter the Secret Key copied from Duo.
-
Enter the Client secret copied from Duo.
-
Click Add Provider.
-
Add an Authentication Profile with Duo as an Authentication Challenge
The authentication challenge selected in this procedure determines which Duo authentication flow users experience at login. Duo Universal Prompt uses the Web SDK application credentials; Duo Auth API uses the Partner Auth API application credentials. For details on how these options map to Duo applications, see Duo Application Types and Authentication Profiles.
For more information, see Creating Authentication Profiles.
-
Navigate to the Authentication profiles page.
-
Click Add Authentication Profile.
-
Enter a profile name.
-
Under Authentication challenges, select Duo Auth API or Duo Universal Prompt and other authentication challenges such as Password, as required.
Enable the Authentication Profile in an Identity Policy
For more information on identity policies and how to set up, edit, and assign them, see Identity Policies.
-
Navigate to the Identity policies page.
-
Select the identity policy that should use Duo.
-
In the Overview section, if the policy is not enabled, select Edit, set the state to Enabled, and click Save.
-
Select Authentication.
-
Next to Services, click Edit.
-
Select Enable authentication policy controls.
-
Click Default authentication profile.
-
From the drop-down menu, select the authentication profile that has Duo configured as an authentication challenge.
-
Click Save.
For more information see Authentication Profiles.
When using authentication rules in identity policies, these rules may override the default authentication profile. For more information, see the Authentication Rules documentation.
Enroll Duo Users
After configuring Duo on the Platform, administrators can invite users to enroll in Duo authentication.
-
In the Duo Admin Console, navigate to Users.
-
Select the desired user.
-
Click Send Enrollment Email. Duo sends the user an email with enrollment links. Users must complete enrollment to receive authentication challenges.
When adding a user to Duo, use the same username and email address the user has on the Delinea Platform.
For details on enrolling users, see the Duo documentation, Duo Administration – Enroll Users.
For details on managing users, see the Duo documentation, Duo Administrators – Manage Users.
Duo Policies
To prevent users who have not yet enrolled in Duo from accessing the Delinea Platform, set the New User Policy to Deny Access.
For details, see Duo's documentation on Users Policy Settings.