Installing the Advanced Session-Recording Agent
Session Recording Metadata Overview
By default, Secret Server session recording creates videos of launched sessions. Secret Server supports logging additional keystroke metadata for RDP and SSH sessions without requiring an agent across both Windows and Mac environments. When these options are enabled, users can search for keystrokes or applications across sessions and the session playback interface displays the additional information.
SSH metadata relies on the Secret Server SSH proxy.
Recording Remote Desktop session metadata requires the installation of an Advanced Session Recording Agent (ASRA) on the target server. In this scenario Secret Server’s protocol handler is still used to launch the session and record the session video, and the ASRA records the metadata only.
ASRA can optionally record any session on the target server. If enabled and the session was not launched from Secret Server, ASRA will record video, keystrokes, and process metadata for the session and upload both to Secret Server once the session is disconnected. This works even if someone logs into the console directly or Remote Desktops into the server without using Secret Server at all. Live viewing of this type of session is not supported.
If you are licensed for session recording, you can install unlimited numbers of ASRAs.
How Advanced Session Recording Agents Work
-
Once the ASRA is installed, it contacts the ASRA callback URL to determine if it should record metadata or video any time someone logs on to the computer.
-
A user logs on.
-
The ASRA sends Secret Server the computer’s hostname, the username of the user who logged on, any domain name if available, and a list of the computer’s IP addresses.
This data is not logged by Secret Server unless you enable DEBUG logging, only for troubleshooting purposes. -
Secret Server checks for any recently-launched protocol handler sessions with matching details, and tells the ASRA if it should record the session.
- If there is a match, the ASRA starts recording metadata and sends it back to Secret Server over the chosen response bus for the duration of the session.
- If there is no match and "Record All Sessions" is enabled for the ASRA, the ASRA records both the video and metadata for the session.
- If there is no match and "Record All Sessions" is not enabled, the ASRA records no video or metadata and waits for the next person to log in.
-
Once a recording session has been closed:
- If the session was launched from Secret Server using the protocol handler, the video from the protocol handler is matched up to the metadata provided by the ASRA and combined.
- If the session was not launched from Secret Server and "Record All Sessions" is enabled, the ASRA uploads both the video recording and the metadata to Secret Server.
-
On the Session Monitoring page, additional icons are presented based on what extra metadata is present for that session, such as keystroke data for both RDP and SSH, and process data for RDP.
-
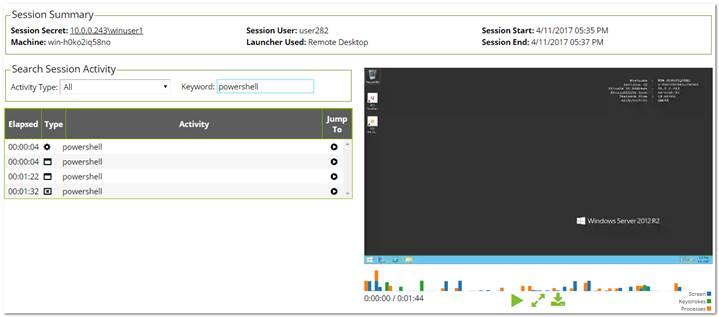
Once the session recording has been processed, on the Session Playback page the additional metadata is visible:
And on the Session Monitoring page:
In this example, we searched for activity where the user typed in the word “PowerShell.”
Record All Sessions
Recording video and metadata for all sessions on a server including console access requires Distributed Engine and ASR to be enabled as described above. ASRA must be installed on the target server, and it must be set to "Record All Sessions." If the server is set to “Only Record Secret Sessions,” the ASRA will only provide metadata when people launch into the server from Secret Server. Secret Server When recording all sessions, they appear on the Session Monitoring page. They are not tied to any specific secret because the sessions are not started by Secret Server.
Secret Server Configuration
First, session recording must be enabled (Admin > Configuration > Session Recording). As that page warns, Delinea highly recommends using RabbitMQ when using session recording in any production environments. See Configuring Session Recording for more information.
SSH Metadata
To record SSH keystroke data, enable the SSH proxy (Admin > SSH Proxy). Individual secrets then require configuration of the Enable Proxy setting and the Enable Session Recording setting. Then when the SSH session is launched and recorded, keystroke data is recorded, which can be searched and is displayed in the session playback interface. See Session Recording Overview and SSH Proxy Configuration for more information.
Remote Desktop Metadata
To record RDP session metadata, first distributed engine needs to be enabled (Admin > Distributed Engine) with an appropriate response bus site connector, which should be a RabbitMQ site connector in production environments. The ASRAs will communicate with the chosen site connector to return any recorded metadata. Next, the Advanced Session Recording feature must be enabled (Admin > Advanced Session Recording), and an ASRA callback URL entered. HTTPS should always be used in production environments. Individual secrets then just need the Enable Session Recording setting enabled, and the computer you launch into must have the ASRA installed. The secrets do not have to use SSH proxy since the ASRA is what records the metadata. See Session Recording Overview for more information.
Session Recording Worker Role
There is a dedicated Session Recording Worker role. If you have a clustered Secret Server environment, you can pick which nodes process recordings on the Admin > Server Nodes page. In a large environment with many recordings, you can configure nodes to be dedicated just to session recording, letting other nodes run the Background Worker and other roles. Session recording processes multiple videos at once, which can be controlled with the PrefetchCount.ConvertVideoMessage AppSetting (default: 2). We recommend setting this AppSetting to half the number of CPU cores on the server as a starting point. This setting applies only when using a RabbitMQ site connector, which is another reason Delinea highly recommends using Rabbit if you are using session recording.
Advanced Session Recording Agent
First, create one or more collections to group the ASRAs together, for example, for different domains or environments. Each collection has a unique installer that you can download from their page – the installer is customized to know which collection it is associated with. On the collection, you can specify if you want new agents to Record All Sessions, or to Only Record Secret Sessions. New agents adhere to this setting, and you can toggle it for individual agents, once they have registered.
Agent Manual Installation
The downloaded installer can be manually installed on a computer by running the setup.exe inside the zip file. It can also be deployed using group policy software installation or other MSI management software.
The ASRA installs itself in C:\Program Files\Thycotic Software Ltd\Session Recording Agent and adds a Windows service, Delinea Session Recording Agent.
Only 64-bit Windows operating systems are currently supported. .NET Core is also required.
Agent Updates
The ASRA does not automatically update, so new versions must be manually installed or re-deployed using the Group Policy MMC.
Agent Uninstallation
You can deactivate specific ASRAs or an entire collection in Secret Server, and the next time the ASRA reaches out to the ASRA callback URL, it will uninstall itself. Since it only reaches out when someone logs on to the computer, it will remain uninstalled until someone logs on again. The ASRA can also be manually uninstalled directly on the computer like any normal Windows application, but then Secret Server will still show it in the list of active ASRAs under its collection. It should also be deactivated in Secret Server to keep the agent list accurate. If "Record All Sessions" is enabled for this server, you will get a prompt to stop the Delinea Session Recorder application when you attempt the uninstall because it is running and recording your session, as expected. To avoid these issues, we recommend using the Deactivate feature in Secret Server and then logging into the machine, and it will uninstall itself on its own.
Agent Group Policy Installation
Task 1: Review the Prerequisites
The ASRA requires a 64-bit operating system with .NET Core or greater installed on the client machine. This is the version that ships with Windows 8.1 and Windows 2012 R2.
Task 2: Download the Advanced Session Recording Agent Installer
-
Log on to Secret Server.
-
Search for Advanced Session Recording.
-
Click on an existing collection, or create a new one, as appropriate.
-
Click the Download Session Recording Installer(64-bit) button. The installer is downloaded to your computer.
The zip file is customized for each collection. Be sure to download the installer from the collection you want your new ASRAs associated with.
Task 3: Customize the Installer
For a normal manual installation, you extract the zip file, and run setup.exe. There are settings saved in setup.exe.config that customize the installation of the MSI file contained in the zip (gsresvc.msi). When you deploy the ASRA using Group Policy software installation instead of a manual one, the only other files in the zip you need is the MSI, which is deployed from a network share, and an MST (Master Software Tools?) “Transform” file which configures the custom settings.
-
Install Microsoft’s free MSI editing tool, Orca, if you do not already have it installed.
-
Extract the ASRA zip file into its own folder.
-
Right click on the MSI file (gsresvc.msi) in the folder where you extracted the zip and select Properties to verify that there is a Digital Signatures tab indicating that the MSI was signed by Delinea Software.
-
Launch Orca.
-
Open the extracted MSI file (gsresvc.msi). The Tables list appears.
-
Click the Transform menu at the top
-
Select New Transform.
-
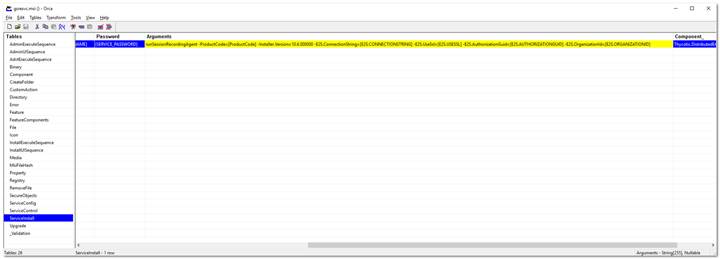
In the Tables list, click ServiceInstall. Only one row should be listed on the right.
This screen shot shows the Arguments column dragged wider to see its contents. When you initially see it, it will be very narrow, barely showing the contents. -
Scroll to the Arguments column and copy and paste its contents into a text editor. It should look like this example. Be sure to select the entire column. You might need to adjust the column width.
The entire string of text is essentially a CLI command with parameters that begin with a hyphen. For illustration purposes we put each parameter on its own line below.runSessionRecordingAgent -ProductCode=[ProductCode] -Installer.Version=10.6.000000 -E2S.ConnectionString=[E2S.CONNECTIONSTRING] -E2S.AuthorizationGuid=[E2S.AUTHORIZATIONGUID]Everything highlighted is what we will customize. The fields in brackets are what setup.exe would normally customize.
-
In your text editor, open the setup.exe.config XML file from the zip. You will get the Globally Unique Identifier (GUID) from it.
-
In your text editor, replace each of these with the correct values as listed below. The GUID will require looking in setup.exe.config in the
XML block. The values are as follows: -
ProductCode should always be: “{A7FA0ADA-BEED-4841-9D3E-9D700B36F653}” (not in setup.exe.config).
-
Installer.Version should match your Secret Server version (visible in Secret Server in the bottom right corner).
-
E2S.ConnectionString is the callback URL for Secret Server Cloud is the Cloud URl.
Secret Server Cloud does not list a Callback URL on the Advanced Session Recording page. -
E2S.AuthorizationGuid is a unique GUID specific to the ASRA collection that you downloaded the installer file from. You can find it in the setup.exe.config file (in setup.exe.config). This is unique for each ASRA Collection.
-
-
Back in Orca, delete everything in the ServiceInstall Arguments column.
-
Copy and paste the customized version you just created from your text editor into the Arguments column.
-
Click the Transform menu.
-
Click Generate Transform.
-
Save the file as
gsresvc.mstin the directory you extracted the installer into. This transform file now contains your customizations for the ServiceInstall Arguments. -
Close Orca.
-
Check the MSI file’s digital signature again to ensure that it was not edited: If you right-click the MSI file and select Properties again, the Digital Signatures tab should still show that the MSI is signed by Delinea Software. You created your own custom MST transform file, but the MSI itself should be unchanged. Orca can edit the MSI file itself, but that will invalidate Delinea’s digital signature and it is unnecessary.
Task 4: Set up a Network Share
-
Place the
gsresvc.msiandgsresvc.mstfiles on a network share on your domain controller. -
Give “Authenticated Users” read access to this share.
Computers in the domain will access this network share to get the installer files before any users log into the machine. It will be the machine account authenticating to the network share, before any users have logged in.
Task 5: Create a Group Policy with Software Installation to install the MSI
-
Open the Group Policy Management Console (Start\ > Administrative Tools > Group Policy Management).
-
Expand the Forest and Domain nodes until you locate the domain on which you are installing the ASRA.
-
Right click on Group Policy Objects and click New.
-
Enter a descriptive name for your GPO, such as “ Delinea Session Recording Agent Installation," and click OK.
-
Right click on the newly created GPO node and click Edit.
-
Select Computer Configuration > Policies > Software Settings > Software Installation.
-
Right click on the Software Installation node and select New > Package.
-
Browse to the MSI on your network share using the share’s UNC path, not its folder path. For example:
\\ServerMachineName\Shared and not C:\Shared. -
Click Open.
-
Click to select the Advanced option button.
-
Click OK. The name is automatically be set to “Delinea Session Recording Agent”, since that is the product name in the MSI file.
You can customize the name here, but if you use something else, that is what you will want to check for in the Verify Configuration section, instead of “Delinea Session Recording Agent.” -
On the Modifications tab, click Add and select your MST transform file. Be sure to again use a UNC path like
\\ServerMachineName\Shared, not C:\Shared.If you wish to have the ASRA uninstalled when it falls out of management, click on the Deployment tab and click to select the box next to “Uninstall this application when it falls out of the scope of management”. -
Click OK.
-
In the group policy object editor, expand Computer Configuration > Administrative Templates > System.
-
Click the Logon node.
-
Right-click Always wait for the network at computer start-up and logon and select Properties.
-
Click Enabled.
-
Click OK. This helps reduce the number of reboots required for this policy to take effect as noted in the description of this option.
Task 6: Link your Group Policy Object to an OU
-
Open the Group Policy Management Console (Start > Administrative Tools > Group Policy Management)
-
Expand the Forest and Domain nodes until you locate the domain on which you are installing the Secret Server protocol handler.
-
Right-click the Organizational Unit (OU) for which you want Secret Server protocol handler to be installed and select Link an Existing GPO.
-
Select the GPO you created earlier.
-
Click OK. The GPO is now linked the entire OU.
To immediately force the group policy change and install the software on a client machine, open a command console on the client machine (start > run > cmd), typegpupdate /force, and restart the client machine. You can also wait for the group policy to go into effect, which usually takes one to two hours, but a reboot will still be required due to the mechanics of group policy software installations.
Task 7: Verify Configuration at the Domain Level
- Go to Start > Administrative Tools > Active Directory Users and Computers.
- Right-click the OU for which Secret Server Protocol Handler is now configured and select All Tasks > Resultant Set of Policy.
- Check to select the box next to Skip to the final page of this wizard without collecting additional information.
- Click Next twice.
- Click Finish.
- In the new Resultant Set of Policy window, expand Software Settings under Computer Configuration.
- Click to select Software installation.
- Delinea Session Recording Agent should be visible in the Installed Applications column.
Task 8: Verify the Configuration of a Domain Member
- From a command prompt, run
gpresult /h report.htmlto output a report for just that one computer to the specified HTML file, which you can then view in a browser. - The Delinea session recording agent should be visible in the Installed Applications section.
- Once the computer has rebooted and completed the installation, the software shows up in Apps and Features (Add Remove Programs). As usual, the Delinea Session Recording Agent Windows Service is installed in
C:\Program Files\Thycotic Software Ltd\Session Recording Agent.