Enabling Launchers
Introduction
By default, the launcher is enabled by the Enable Launcher setting on the Configuration page.
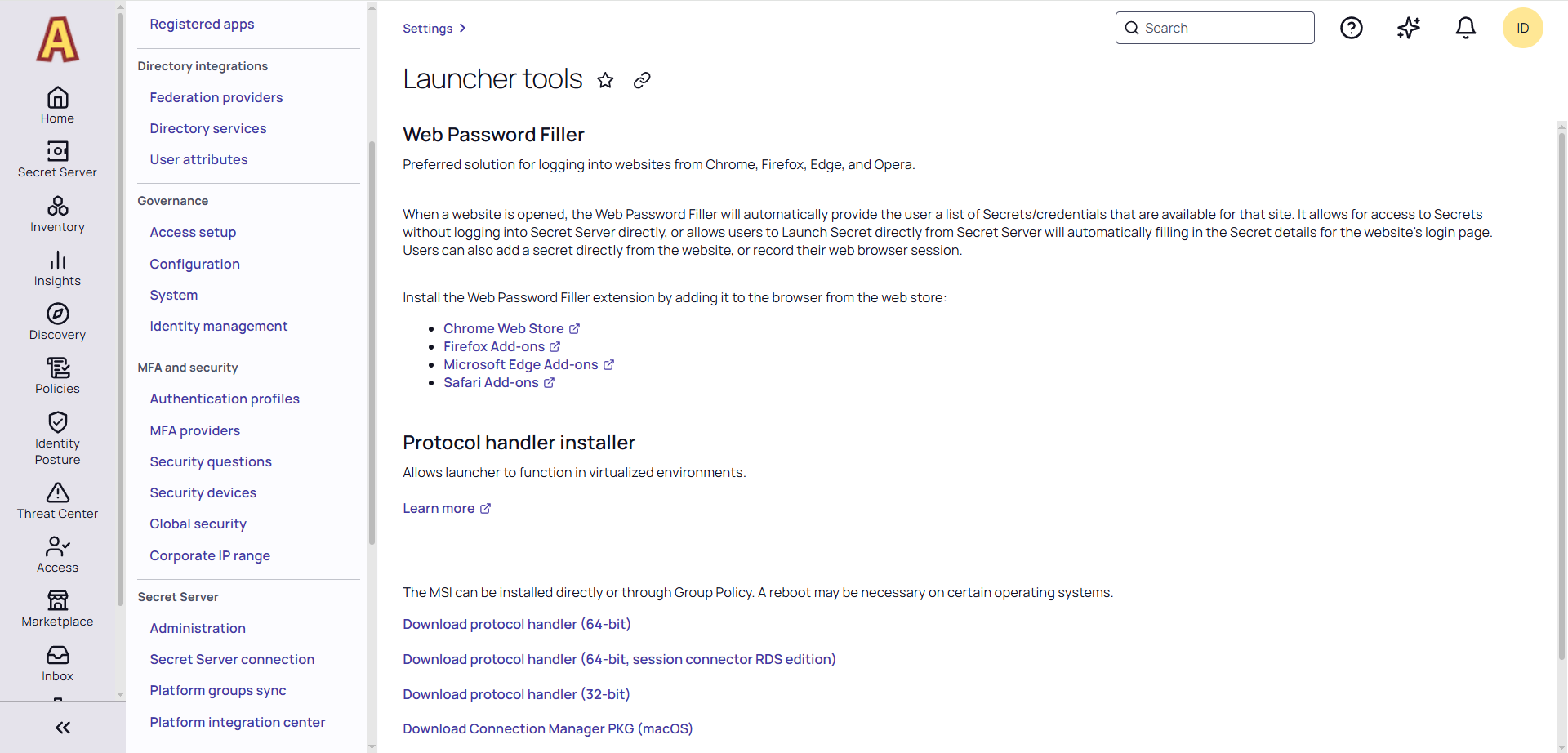
The launcher (protocol handler) can be deployed in two ways—with the Protocol Handler MSI installer (recommended) or ClickOnce. This can also be set in the configuration settings. The MSI installer allows the launcher to be used in virtualized environments or any environment in which the user does not have access to a Windows Temp directory. The Protocol Handler can be downloaded by clicking one of the links under the Protocol Handler section:
MSI Installer
To use the MSI installer (protocol handler installer) following steps below:
-
Select Settings.
-
In the Tools and Integrations section, click Launcher Tools.
-
In the section labeled Protocol Handler Installer, select the Download Protocol Handler MSI link for the operating system you want to install on.
-
Run the MSI file with admin privileges.
Installing by Group Policy
The Protocol Handler application runs without requiring any input from the user. The installation may be pushed to your network without any special configuration.
Securing the Protocol Handler
Protocol Handler security is a frequent topic in penetration tests and vulnerability assessments. The following mechanisms help ensure that only trusted Secret Server URLs can trigger launches.
First-Time URL Verification
When the Protocol Handler connects to a Secret Server URL for the first time, it prompts the user to confirm whether the URL is legitimate.
-
If the user confirms the URL is legitimate: The launch proceeds normally. The URL is trusted for future launches on that machine.
-
If the user rejects the URL: The URL is blocked on that machine. All subsequent launch attempts from that URL will fail with an error message.
Administrative Control via Registry Key (Allowed Domains)
Administrators can manage allowed Secret Server URLs centrally using a registry key, bypassing the per-user prompt entirely. This is the recommended approach for enterprise environments.
Registry key path:
HKLM\Policies\Thycotic\ProtocolHandler\AllowedDomains
To configure allowed domains:
-
Navigate to the key above (create it if it does not exist).
-
Add one or more string values under the key, where each value is the URL of an allowed Secret Server site.
Behavior:
-
If any values are present in this key, only the URLs listed will be permitted. All other URLs will be blocked.
-
If the key is empty or does not exist, the per-user prompt (described above) is used instead.