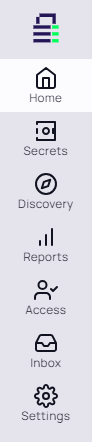
Main Navigation Drawers
Introduction
For version 11.7, Secret Server's left navigation was greatly enhanced. The adminstration side panel was removed and replaced by a more all-emcompassing drawer-like nested navigation panel:
Figure: Main Navigation Drawers
You access it by clicking or hovering over the desired menu item or clicking the >> icon at the bottom. Clicking the << icon closes the selected drawer.
Home Drawer
The home drawer contains the Application Dashboard.
Secrets Drawer
All Secrets
All Secrets displays all secrets that the user has permission to view. It provides a comprehensive list of all the secrets the user can access within Secret Server.
Quick Access
Quick access provides a convenient view of high-use secrets as well as keeping track of secrets that have been opened during the current session. It allows users to quickly find and access secrets they use frequently.
Favorites
Users can mark secrets as "Favorites" for easy retrieval. This feature allows users to quickly access secrets they use regularly without having to search for them each time.
Recent
This link shows the 15 secrets accessed most recently by the user. It helps users quickly return to secrets they have worked with in the near past.
Most Used
This link displays the secrets that the user has opened most often, providing quick access to the secrets that are most important or frequently needed in their daily tasks.
Shared with Me
This link shows the secrets that other users have shared with the user. It allows for collaboration and sharing of necessary credentials without compromising security, as permissions are still enforced.
Checked Out
The "Require Check Out" feature ensures that only one user at a time has access to a secret. When enabled, users must check out a secret before they can access it, preventing other users from accessing the secret while it is checked out.
Folders
The Folders section contains the Folders
Discovery Drawer
Analysis
Opens the Discovery page to the Analysis tab. The analysis feature in Secret Server discovery provides a graphical summary of discovery activity, allowing users to manage discovered items effectively. It includes information about each item and is crucial for managing the discovered items. Items from disabled discovery sources will not be visible.
Network View
Opens the Discovery page to the Network View tab. The network view allows users to view the results of completed discovery after defining the discovery sources. It provides a graphical representation of the organizational structure and allows users to filter items by type, such as computers, computer accounts, public keys, service accounts, or directory accounts. Users can also initiate a rescan of certain items like computers by clicking the scan button.
Sources
Opens the Discovery page to the Sources tab. Discovery sources are the starting point for the discovery process. They define where and how Secret Server should look for accounts and dependencies.
Log
Opens the Discovery page to the Log tab. The discovery log provides a detailed record of the discovery process. It logs the activities and events that occur during the discovery scans, including the identification and categorization of computers, accounts, and dependencies within the network. The log is useful for troubleshooting, auditing, and understanding the actions taken by the discovery feature.
When a discovery scan is run, whether manually or automatically, the discovery log captures information such as:
-
The start and end times of the discovery scan.
-
Any errors or issues encountered during the scan.
-
Details about the objects that were discovered, such as computers and accounts.
-
Actions taken by the discovery process, such as creating new secrets for discovered accounts or linking discovered dependencies to existing secrets.
By reviewing the discovery log, administrators can gain insights into the effectiveness of the discovery scans, identify any potential issues that need to be addressed, and ensure that the discovery process is functioning as intended. It serves as a historical record that can be referenced to verify the discovery activities and outcomes.
Computer Scan Log
Opens the Discovery page to the Computer Scan tab. The computer scan log shows logs of the computer scanning process. This log provides details about the scanning of each machine found during the discovery scan to collect information configured to be collected by the discovery source.
Computer Scan Results
Opens the Discovery page to the Computer Scan Results tab. The computer scan results feature provides detailed information about the scanning process. It includes the results of the computer scan, which attempts to collect information such as local accounts, Windows services, scheduled tasks, and IIS application pools from each machine found during the discovery scan.
Reports Drawer
Report List
Opens the Reports page to the General tab, which contains the report list. The list provides a set of standard reports that include a variety of 2D and 3D charting and graphing components, as well as full grids of data. Some reports are purely data detailed and have no charts. Users can create custom reports based on Secret Server data such as user, audit, permissions, and folders. Reports can be organized into categories to aid in organization and access control.
Security Hardening
Opens the Reports page to the Security Hardening tab. The security hardening report checks aspects of Secret Server to ensure security best practices are being implemented. It identifies potential security issues within an installation and provides recommendations for hardening the security posture of the Secret Server environment.
User Audit
Opens the Reports page to the User Audit tab. The user audit report feature in Secret Server displays every password or secret accessed by a user within a specified period. This report is essential for assessing and controlling vulnerability risk when someone leaves the organization and for complying with regulatory requirements.
Schedules
Opens the Reports page to the Scheduled Reports tab that allows users to set reports to be generated on a regular schedule and sent via email to the management team or auditors. With the Health Check option, users receive an email only when a report has content, targeting unusual events for immediate alerts.
Audit
Opens the Reports page to the Audit tab. Secret Server maintains an immutable audit log of privileged user activity, which can be reviewed by the IT and security team. The audit feature includes customizable alerts (Event Subscriptions) that send email notifications when specified actions are performed or events occur. Audit reports provide accurate details on the secret itself, allowing users to monitor the level of activity on any secret they have access to.
Access Drawer
Users
Opens the Users tab of the User Management page. Secret Server supports both Local and Domain user accounts for authentication. Local user accounts are stored and managed by Secret Server, while domain user accounts are managed by Active Directory but subject to changes made in Secret Server. Administrators can create, edit, or remove local user accounts and configure account lockout settings to prevent repeated unsuccessful login attempts.
Groups
Opens the Groups tab of the User Management page. Secret Server allows administrators to manage users through user groups. Users can belong to different groups and receive the sharing permissions and roles attributed to those groups. This setup simplifies the management of permissions and roles that can be assigned to a user. Groups can also be synchronized with Active Directory.
Roles
Opens the Roles tab of the Roles Page. Role-Based Access Control (RBAC) in Secret Server enables IT admins to control what individual users can do within the application. Secret Server ships with out-of-the-box roles for common configurations and allows custom roles to be created that correspond to an organization's structure.
Directory services
Opens the Domains tab of the Directory Services page. Secret Server integrates with Active Directory, allowing administrators to automatically grant and revoke access to Secret Server with existing tools and policies. By assigning access based on security groups, manual permission granting is minimized, and users' rights in Secret Server change appropriately when their roles change.
IP address restrictions
Opens the Overview tab of the IP Address Management page. IP address restrictions in Secret Server allow administrators to control the locations and networks from which users can gain access. This feature enables limiting access to Secret Server to users who are "on network" and not accessing through VPN or other external networks.
Inbox Drawer
Secret Access Requests
Opens to Inbox > Secret Access Requests. The secret access requests feature in Secret Server allows a secret to require approval before access is granted. When a user requests access to a secret, an email is sent to the approval group(s), notifying them of the request. Members of the approval groups can approve or deny the request, and access can be granted for a set time period. This feature establishes a workflow model where users must request access, and approvals can be managed through the Secret Server interface or via email if configured.
Secret Erase Requests
Opens to Inbox > Secret Erase Requests. Secret erase requests are used when a secret needs to be permanently removed from Secret Server. This is typically done for regulatory compliance and is not intended for database cleanup. When a secret erase request is made, it must be approved by designated approvers before the secret can be erased after a specified date and time. The process ensures that irreversible actions are taken with proper authorization and for valid reasons.
Application Requests
Opens to Inbox > Secret Application Requests. Application requests are not explicitly mentioned in the provided documents. However, in the context of Secret Server, this could refer to requests related to application account secrets or requests for integrating applications with Secret Server. These requests would likely follow a similar approval process to ensure proper access control and security compliance.
System Alerts
Opens to Inbox > System Alerts. System alerts are notifications that inform administrators and users about important system events or conditions that require attention. These can include alerts about system health, configuration changes, heartbeat failures, or other significant system-related issues. Alerts can be customized and sent via email to ensure prompt awareness and response.
Notifications
Opens to Inbox > Notifications. Notifications can include alerts about access requests, system events, and other important information that users need to be aware of.
Rules (Management)
Opens the Rules tab of the Inbox > Notifications page. Inbox rules are used to trigger actions based on notifications and can send either an email or a Slack message to a specified group of users when certain conditions are met. These rules are primarily for non-admin end-user communications and event subscriptions. They are used to filter notifications and define who receives the email or Slack message when a notification arrives.
Templates (Management)
Opens the Templates tab of the Inbox > Notifications page. Inbox templates are used for formatting and populating the content of messages sent to users' inboxes and can also be used by event pipelines. These templates define the subject, language used, and the canned text for the message, which contains variables that are replaced by Secret Server when the message is sent. Inbox templates can be system templates, which are read-only and can be cloned to create custom templates, or they can be custom templates that users create and edit themselves.
Inbox templates are crucial for managing how email and notifications are sent and received by users. They allow for configuration of notification scheduling, collecting notifications into digest format, and creating message templates and rules. This customizable tool set helps reduce alert fatigue by enabling users to receive notifications in a way that is most relevant and actionable for them.
Resources (Management)
Opens the Resources tab of the Inbox > Notifications page. Resources associated with inbox templates are items, such as images, that go along with any email based on the template. These resources are included in the message to enhance the visual presentation and provide additional context or branding.
Settings Drawer
All settings
Opens the Admin > All Settings page in the alphabetical view. This page serves as a comprehensive list of all system settings, organized alphabetically for easy navigation. This page allows administrators to quickly locate and manage various configurations, from authentication methods to email settings, ensuring that they can fine-tune the Secret Server environment to meet their organization's specific security and operational requirements.
Configuration Search
Opens the Admin > Search (for a) Configuration page. This page is a utility within Secret Server that enables administrators to swiftly find any system configuration by entering search terms. This feature streamlines the process of locating specific settings among the multitude of configurable options, saving time and simplifying system management tasks.
Sites and Engines (Distributed Engine)
Opens the Sites and Engines tab of the Distributed Engine page. This tab provides an overview and management interface for the distributed engines and their associated sites within Secret Server. This tab allows administrators to configure and monitor the engines that handle tasks such as remote password changing and discovery scans, ensuring efficient distribution of workload across the network.
Configuration (Distributed Engine)
Opens the Configuration tab of the Distributed Engine page. This tab is where administrators can set up and modify the settings for distributed engines in Secret Server. This tab includes options for engine registration, task assignment, and communication settings, which are crucial for the engines to operate correctly and securely within the distributed architecture.
Audit (Distributed Engine)
Opens the Audits tab of the Distributed Engine page. This tab offers a detailed log of all activities related to distributed engines, providing administrators with a transparent view of engine operations. This audit trail is essential for security and compliance, as it records actions such as engine registration, task execution, and any configuration changes.
SSH (Proxying)
Opens the SSH Proxy tab of the Proxying page. This tab allows administrators to configure the settings for SSH proxying within Secret Server. This tab includes options to enable the proxy, set the proxy port, and manage other related settings, which are vital for securely routing SSH sessions through Secret Server and protecting endpoint credentials.
RDP (Proxying)
Opens the RDP Proxy tab of the Proxying page. This tab is dedicated to configuring the RDP proxying feature in Secret Server. Administrators can enable the RDP proxy, define the proxy port, and adjust settings to ensure that RDP connections are securely routed through Secret Server, enhancing credential security and session management.
SSH Terminal (Proxying)
Opens the SSH Terminal tab of the Proxying page. This tab provides configuration options for the SSH terminal within Secret Server. This tab allows administrators to customize the terminal settings, such as enabling command menus and setting up session recording, to ensure a secure and controlled environment for SSH sessions.
Endpoint Configuration (Proxying)
Opens the Endpoints tab of the Proxying page. This tab lists all the server nodes, sites, and engines that can be configured as proxies for SSH and RDP sessions. Administrators can manage which nodes act as proxies and configure their public host and bind IP addresses, ensuring that sessions are securely routed through the designated endpoints.
Configuration (RPC)
Opens the Remote Password Changing page. This page is where administrators configure and manage the remote password changing feature in Secret Server. This page allows for the setup of password changers, scheduling of password changes, and monitoring of password change activities, which are critical for maintaining password security across the network.
Password Changers (RPC)
Opens the Password Changers Configuration page. This page is a central location for setting up and managing the password changers used in Secret Server. Administrators can add, edit, and delete password changers, as well as configure their settings to ensure that passwords are changed according to organizational policies and compliance requirements.
Dependency Changers (RPC)
Opens the Dependency Changers page. This page is designed for administrators to configure and manage the dependency changers in Secret Server. This page enables the setup of dependencies for secrets, ensuring that related credentials are updated in sync when a password change occurs, maintaining consistency and reducing the risk of service disruptions.
Heartbeat Log (RPC)
Opens the Heartbeat Log tab of the RPC Logs page. This tab provides a log of all heartbeat activities within Secret Server. Administrators can review the log to monitor the health and accessibility of secrets, ensuring that credentials are valid and services are operational, which is essential for maintaining system integrity.
Password Change Log (RPC)
Opens the Password Change Log tab of the RPC Logs page. This tab offers a detailed record of all password change activities in Secret Server. This log is crucial for tracking the success or failure of password changes, troubleshooting issues, and ensuring that password policies are enforced across the organization.
Secret Policy (General)
Opens the Admin > Secret Policy page. This page is where administrators create and manage secret policies in Secret Server. These policies define sets of rules that can be applied to multiple secrets, such as remote password changing and security settings, to enforce consistent security requirements across the organization's secrets.
Secret Templates (General)
Opens the Templates tab of the Admin > Secret Template page. This tab provides a list of all secret templates available in Secret Server. Administrators can create, edit, and manage templates, which dictate the structure and policies of secrets, ensuring that sensitive information is stored and handled in a standardized and secure manner.
Event Pipeline Policy (General)
Opens the Policies tab of the Admin > Event Pipelines page. This page allows administrators to create and manage event pipeline policies in Secret Server. These policies define the workflows and actions triggered by specific events, enabling automated responses to activities within the system and enhancing operational efficiency.
Event Subscriptions (General)
Opens the Subscriptions tab of the Admin > Event Subscriptions page. This tab is where administrators can set up and manage event subscriptions in Secret Server. This feature enables the configuration of notifications for defined events, which are sent to users' inboxes and can be further communicated externally via email or Slack, keeping stakeholders informed of critical activities.
Workflow (General)
Opens the Admin > Workflows page. This page is dedicated to creating and managing workflows in Secret Server. Workflows allow for the setup of multi-tiered approval processes for secret access, providing a structured and secure method for sharing sensitive information within the organization while maintaining control and auditability.