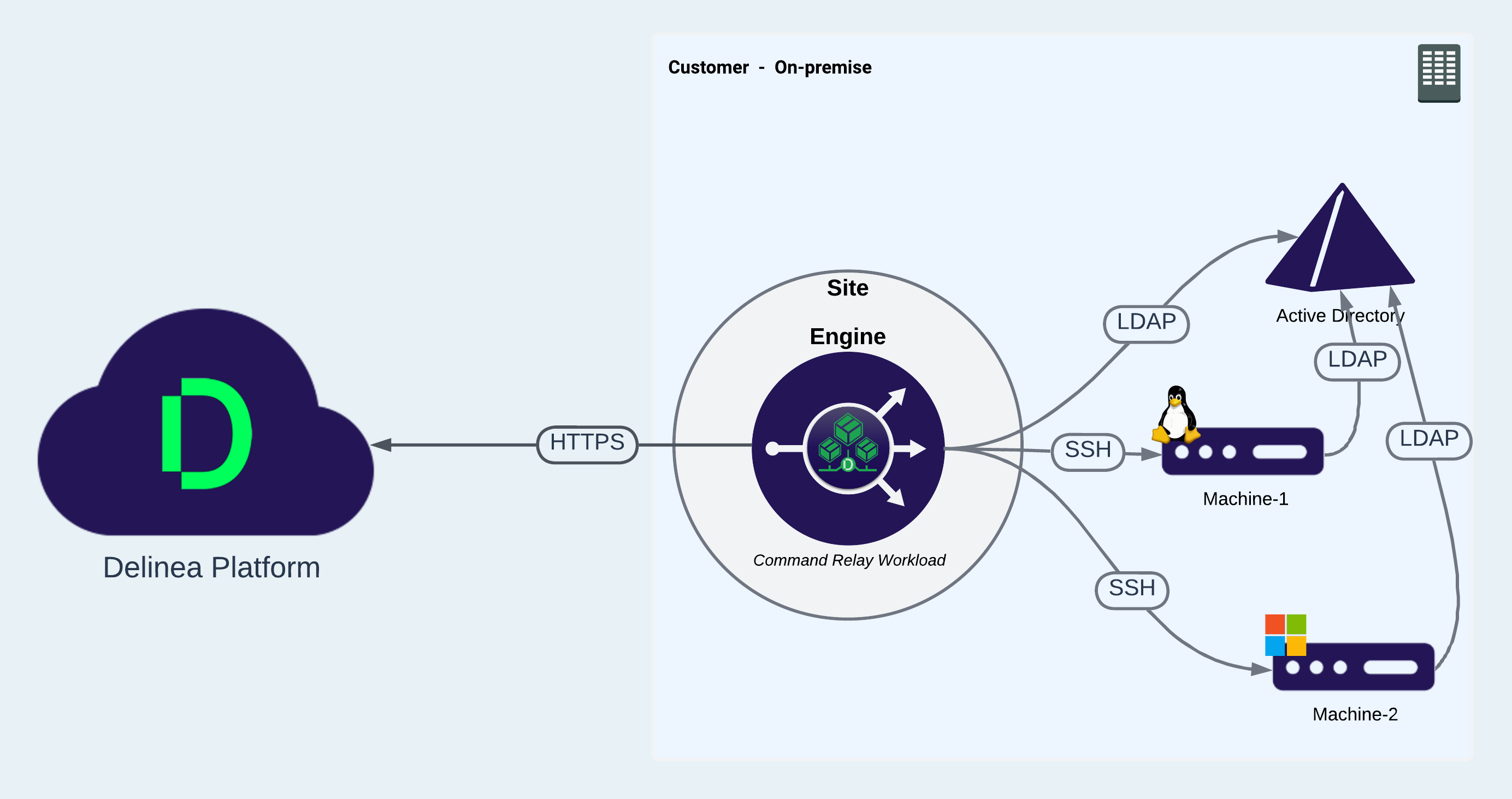
Command Relay Workload
The command relay workload is a service that facilitates communication between the customer and the Delinea Platform through an SSH connection. Its primary function is to dispatch commands along with their parameters to be executed within the customer's environment. The command relay requires a service account that can modify your domain so the proper administrative policies can be added.
Command Relay Prerequisites
-
.Net 4.8 - must be installed on the Platform Engine target machine.
.NET 4.8 is pre-installed on Windows 2022 servers. If you are using an earlier Windows OS and .NET 4.8 is not installed, Command Relay installs it automatically. In this case, you need to reboot the server.
-
Active Directory Web Services (ADWS) must be running on the DC.
-
Port 9389 must be open from the Command Relay machine to the Windows Active Directory domain controller (DC).
Command Relay activates the PowerShell module on the Windows Server machine, and it downloads and installs the PowerShell feature required by Command Relay.
Editing Command Relay Settings
To execute the Command Relay workload, a Command Relay Service account must be selected. Follow the steps below to add the account. The user will only see accounts for which they have permissions.
-
Navigate to the Engine Management page.
-
Select a site.
-
Click the Settings tab.
-
In the Command Relay workload pane, click Edit (pencil icon).
The first time this settings page is opened, the Command Relay Service Account shows None.
-
Click Select.
-
Search for the vaulted account where you have permissions, and select the account.
-
The logged-in user must be the owner of the secret for the account.
-
The secret must not be configured for checkout.
-
-
Select Turn off folder inheritance and Share Secret. This disables inheritance, granting workloads access to the secrets.
-
Click Save after the domain is selected.
| Setting | Description |
|---|---|
| Domain | User should be able to select the Domain accounts they already have access to |
Command Relay Account Permissions
On the server where you will install the Platform Engine and the Command Relay workload, define a service account for Command Relay, then configure the account with local server permissions, domain permissions, or domain administrator permissions (temporary) as described in those sections below.
Local Server Permissions
With local permissions on the server where the Platform Engine and Command Relay will be installed, the Command Relay service account can create the DelineaPlatform OU manually before running the setup for Command Relay. The local server permissions must include the Log on as a batch job permission to allow PCS to work.
Assign the Log on as batch job permission
To assign the Log on as a batch job permission to the Command Relay service account, follow these steps:
-
Select Local Computer Policy > Computer Configuration > Windows Settings > Security Settings > Local Policies > User Rights Assignment.
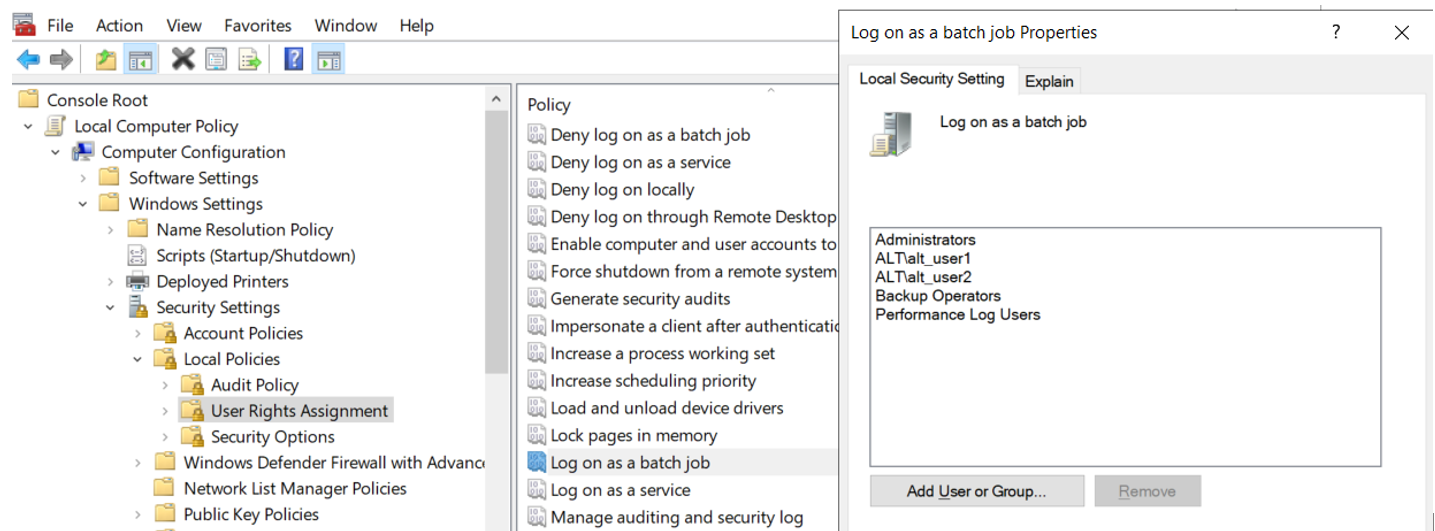
-
Select the Log on as a batch job permission.
-
On the Local Security Setting tab, click Add User or group.
-
Navigate to and select the Command Relay service account to apply the permission.
The Log on as batch job permission is granted by default to all members of these three AD groups:
- Administrators
- Backup Operators
- Performance Log Users
Domain Permissions
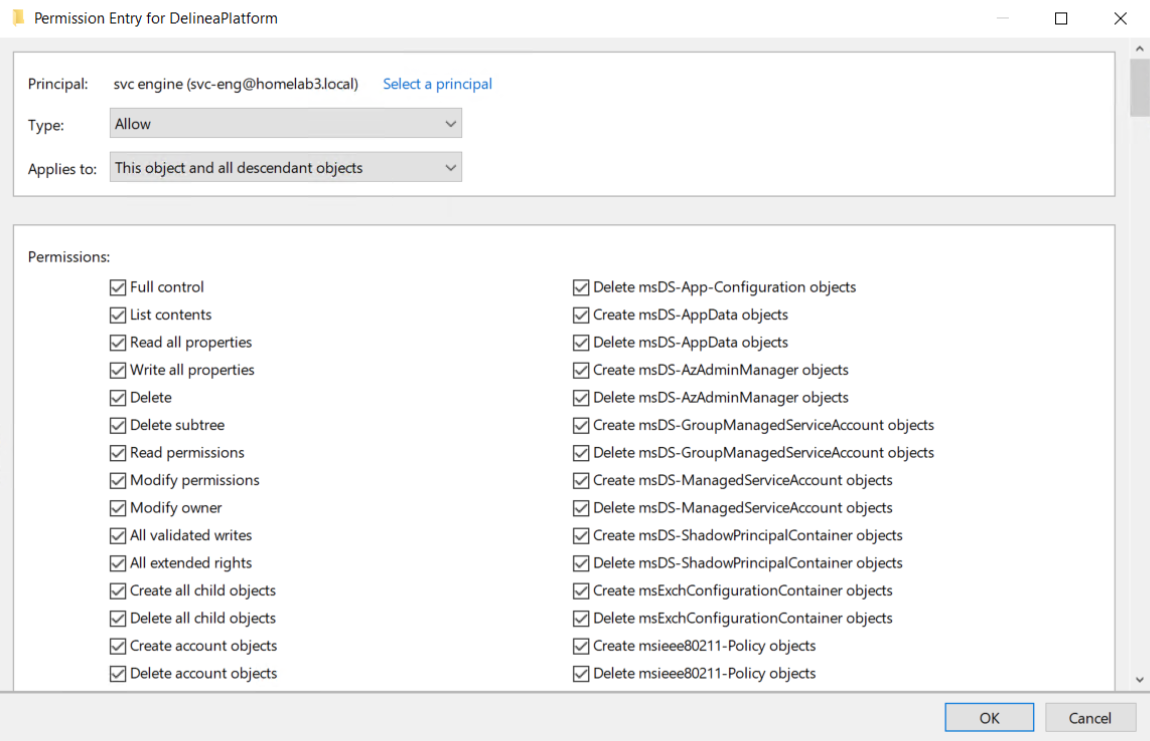
An object named OU=DelineaPlatform must be created at any desired location in the domain. Permissions giving Full Control to create the OU=DelineaPlatform object and all child objects must be given to the Command Relay service account. In the Permissions section of the Permission Entry dialog, every checkbox must be selected, as shown in the following image.
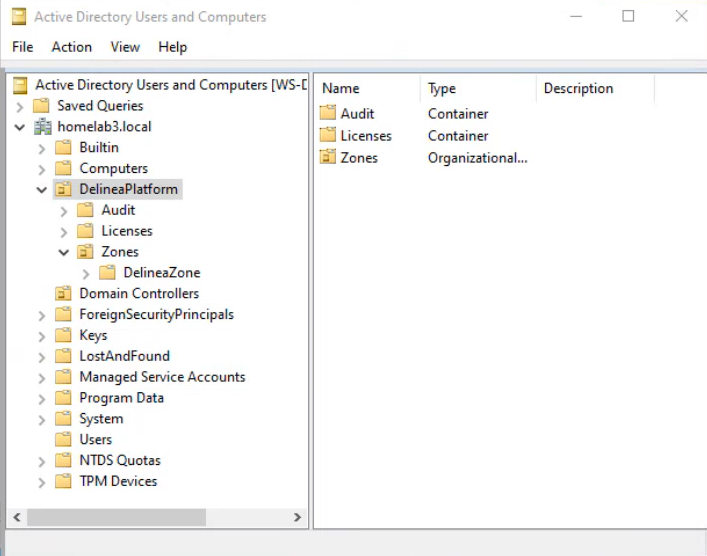
The DelineaZone
When Command Relay executes, it creates the DelineaZone within the DelineaPlatform OU, as shown in the following image.
The DelineaZone contains all the agent policies that need to be enforced on applicable servers. The DelineaZone is managed by the platform.
Minimum Permissions to Join a Server to a Zone
The minimum permissions required to join a server to the DelineaZone depend on the operating system.
Windows
The minimum permissions for an AD user or group to join a Windows server to the DelineaZone:
-
Local Administrator permissions on the server
-
AD Permissions:
-
Create all child objects
-
Generic Read
-
*nix
The minimum permissions for an AD user or group to join a *nix server to the DelineaZone:
-
Root permissions on the server
-
AD Permissions: Create AD Computer Object
-
AD Permissions: DelineaZone:
-
Create all child objects
-
Generic read
-