OTP Client Authentication
Organizations can enhance security by implementing OATH OTP-based authentication alongside standard password-based login for local Delinea Platform accounts.
This topic outlines the steps to enable users to enroll and log in to theDelinea Platform using an OTP client as a Multi-Factor Authentication (MFA) mechanism.
The same approach can be extended to users from external directories, such as Active Directory (AD), though some additional configuration may be required. The platform’s identity policies and authentication profiles provide extensive flexibility, enabling organizations to design authentication workflows that meet their specific security and operational needs—going beyond the basic setup described in this topic.
Creating a Group for OTP Users
-
Navigate to Access > Groups.
-
Click Add Group and provide a name (e.g., OTP-group).
Defining an Identity Policy for OTP Authentication
An identity policy enforces authentication rules for users. Configure an OTP-based identity policy and assign it to the group.
-
Navigate to Access > Identity policies.
-
Click Add Policy and provide a name (e.g., OTP-policy).
-
Assign the identity policy to the group (e.g., OTP-group).
-
At a minimum, configure the policy with the following settings:
-
Navigate to the Authentication tab.
-
In the Services section, click Edit.
-
Select Enable authentication policy controls.
-
Set (or create) a Default authentication profile with the following authentication mechanisms:
-
Challenge 1: Password
-
Challenge 2: OATH OTP client
-
-
Click Save.
-
-
Under Other Settings, click Edit.
-
CheckAllow users without a valid authentication factor to log in and Save.NOTE on using MFA with OATH OTP for new users: This setting is not enabled by default, but it must be enabled to allow new users to access the platform to set up their second authentication challenge. If this setting is not enabled, new users will be advised that they need an additional authentication challenge to log in.
-
Enable this option to allow new users to access the Platform to set up their second MFA challenge. If this option is not enabled, users will be notified they lack the attributes required to log in.
-
Enable this option to allow new users to access the Platform before fully onboarding their OTP client (after the user accepts the initial invite – see later steps).
-
-
-
Under User Security > OATH OTP tab, click Edit.
-
Enable OATH OTP integration to allow users to authenticate using an OTP client, and Save.
-
-
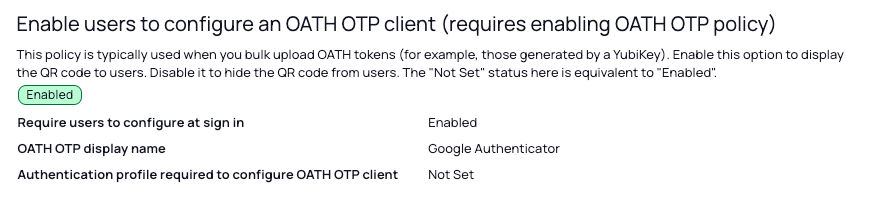
Under User Security > Authentication settings, click Edit.
-
Enable Enable users to configure an OATH OTP client (requires enabling OATH OTP policy).
-
Enable Require users to configure at sign-in. This forces users to enroll their OTP client during onboarding before gaining full access to the Platform.
-
Specify an OATH OTP Display Name (e.g., Google Authenticator).
-
-
Creating and Onboarding an OTP User
Once the identity policy is set up, create a test user and verify the onboarding flow.
-
Create a local user (e.g., OTP-user@domain).
-
Assign the user to the OTP user group (e.g., OTP-group).
-
The user will receive an invitation email to join the Delinea Platform.
-
After accepting the invitation, the user will be required to set a password during their first log-in.
-
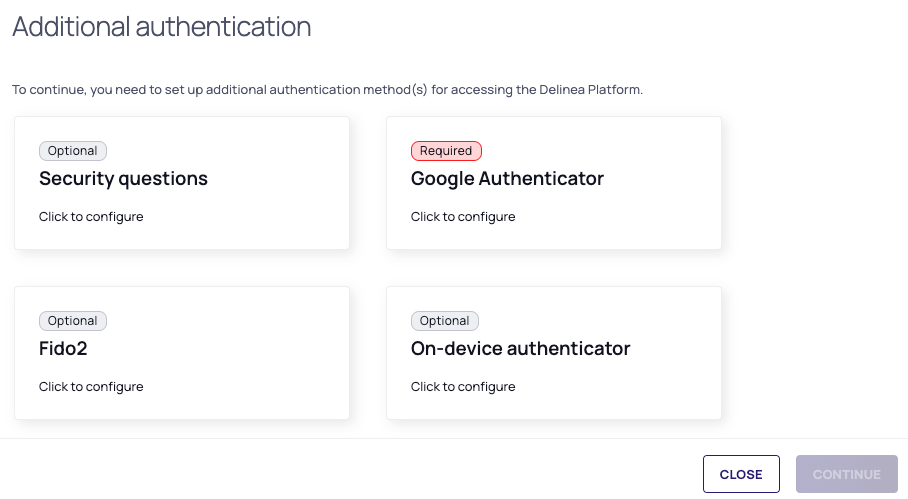
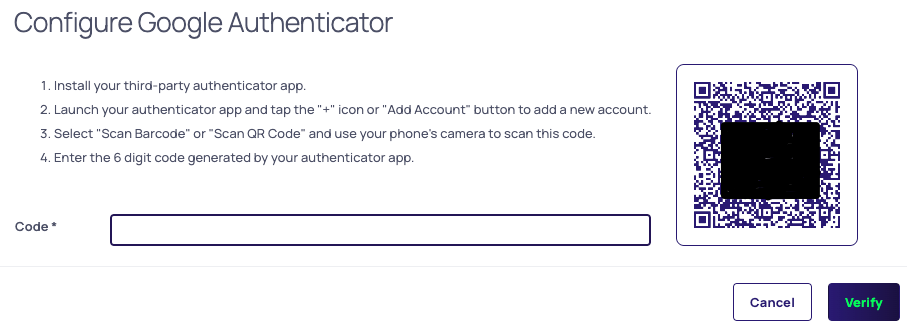
The user will then be prompted to enroll their OTP client (e.g., Google Authenticator).
-
The user will scan the QR code generated by the platform and follow the steps provided to complete the enrollment.
Platform Login Flow
Next time the user tries to login to platform they will follow these steps:
-
Enter their username and password.
-
When prompted, enter the OTP code generated by their OTP client (e.g., Google Authenticator).
-
If authentication is successful, access to the Delinea Platform is granted.
Summary
By implementing OATH OTP-based authentication, users benefit from an additional layer of security while ensuring seamless access management. This approach helps organizations enforce MFA best practices, reducing the risk of unauthorized access to the Platform.